diff --git a/deploy/az/servicefabric/LinuxContainers/readme.md b/deploy/az/servicefabric/LinuxContainers/readme.md
index 5bdd86737..98d097b10 100644
--- a/deploy/az/servicefabric/LinuxContainers/readme.md
+++ b/deploy/az/servicefabric/LinuxContainers/readme.md
@@ -1,83 +1,129 @@
-# Deploying Azure Service Fabric (No Secured)
+# Deploying a Service Fabric cluster based on Linux nodes
-The ARM template `servicefabricdeploy.json` and its parameter file (`servicefabricdeploy.parameters.json`) are used to create a service fabric cluster environment for linux containers.
+## A. Unsecured cluster (SF Linux cluster)
+For a secured cluster, see option B. below.
-## Editing servicefabricdeploy.parameters.json file
+You can always deploy a SF cluster through the Azure portal, as explained in this article: https://docs.microsoft.com/en-us/azure/service-fabric/service-fabric-get-started-azure-cluster
+
+However, when creating a cluster, there are quite a few configurations to take into account, like enabling the internal DNS service or Reverse Proxy service, choosing between Linux/Windows, open/publish your application ports in the load-balancer and most of all (the most complex setup) how to create a secure cluster.
+
+Because of those reasons, we have created a set of ARM templates and scripts so you can create, re-create and configure the SF clusters much faster, as explained below:
+
+Within eShopOnContainers root folder, at the folder [..\deploy\az\servicefabric\LinuxContainers](https://github.com/dotnet-architecture/eShopOnContainers/tree/dev/deploy/az/servicefabric/LinuxContainers), you can find the ARM template `servicefabricdeploy.json` and its parameters file (`servicefabricdeploy.parameters.json`) to create a Service Fabric cluster environment for Linux Containers.
+
+## Edit the servicefabricdeploy.parameters.json file
Edit the following params in `servicefabricdeploy.parameters.json` file to set your values:
- clusterName: Name of your SF cluster
+- clusterLocation: Datacenter location, like westus or westeurope
+- computeLocation: Datacenter location, like westus or westeurope
+- adminUserName: user-name for VMs administration
+- adminPassword: user-password for VMs administration
- dnsName: Name assigned to your SF dns
-- adminUserName: user name for administration
-- adminPassword: user password for administration
-Optionally, you can modify which ports are opened in the LoadBalancer for accessing externally to the apps:
+Optionally, you could modify which ports are opened in the LoadBalancer for the multiple eShopOnContainer apps and API services.
+By default, they are setup as:
+- webMvcHttpPort: 5100
+- webSpaHttpPort: 5104
+- webStatusHttpPort: 5107
+- IdSrvHttpRule: 5105
+- BasketApiHttpRule: 5103
+- CatalogApiHttpRule: 5101
+- OrderingApiHttpRule: 5102
+- MarketingApiHttpRule: 5110
+- LocationsApiHttpRule: 5109
-- webMvcHttpPort: port externally exposed for the WebMVC app
-- webSpaHttpPort: port externally exposed for the WebSPA app
-- webStatusHttpPort: port externally exposed for the WebStatus app
-- IdSrvHttpRule: port externally exposed for the Identity app
-
-## Deploy the template
+## Deploy the Service Fabric cluster using the script and ARM templates
Once parameter file is edited you can deploy it using [create-resources script](../readme.md).
-i. e. if you are in windows, to deploy sql databases in a new resourcegroup located in westus, go to `deploy\az` folder and type:
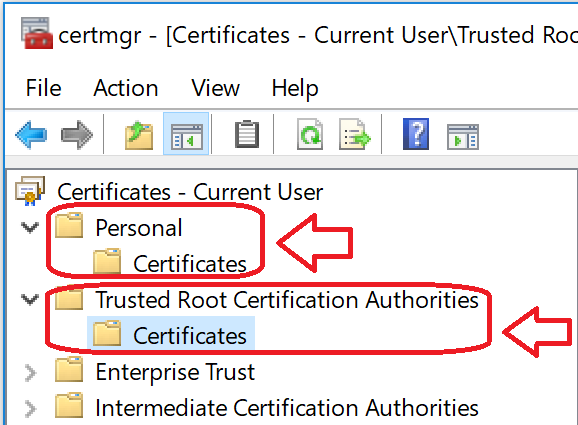
+For example, to deploy the cluster to a new resourcegroup located in westus, go to `deploy\az` folder and type:
```
-create-resources.cmd servicefabric\LinuxContainers\servicefabricdeploy newResourceGroup -c westus
+create-resources.cmd servicefabric\LinuxContainers\servicefabricdeploy qa-eshop-sflinux-resgrp -c westus
```
-## Deploy eShopOnServiceFabric with Visual Studio.
-Alternatively, instead of using ARM templates, you can deploy eShop on service fabric directly by publishing the project eShopOnServiceFabric in eShopOnContainers-ServicesAndWebApps.sln with Visual Studio publish tool.
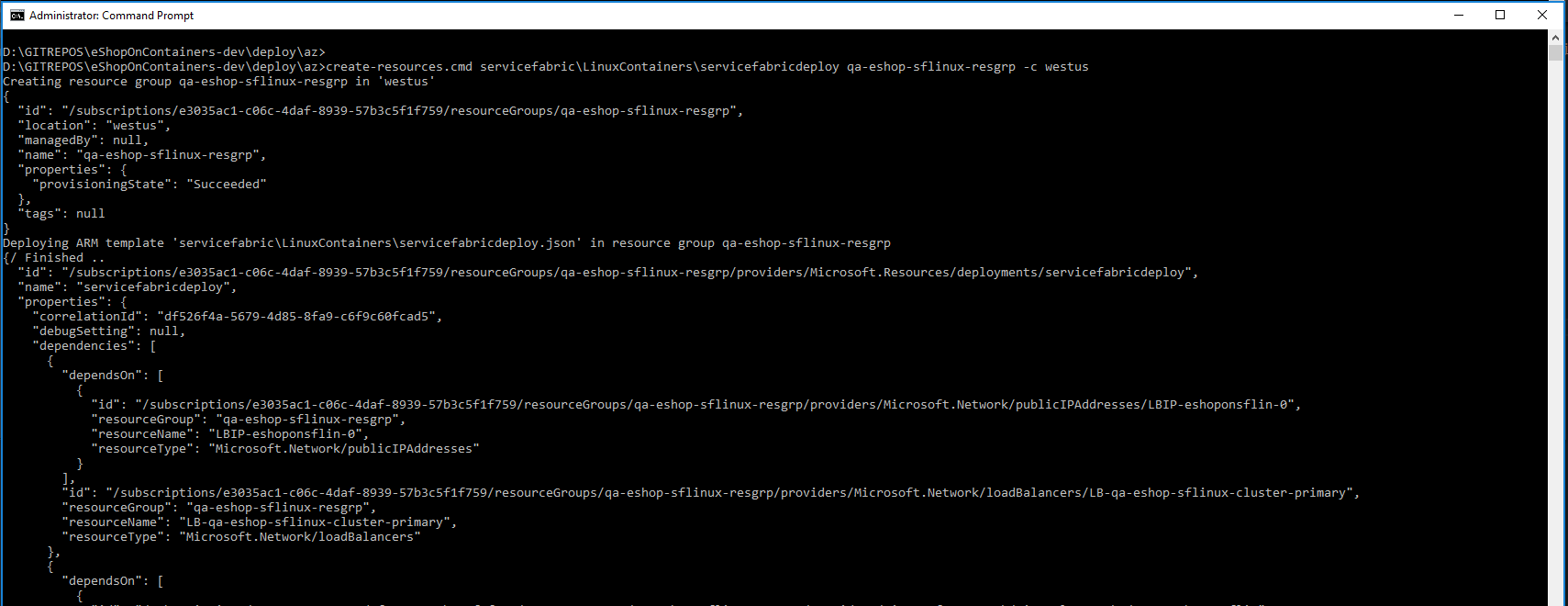
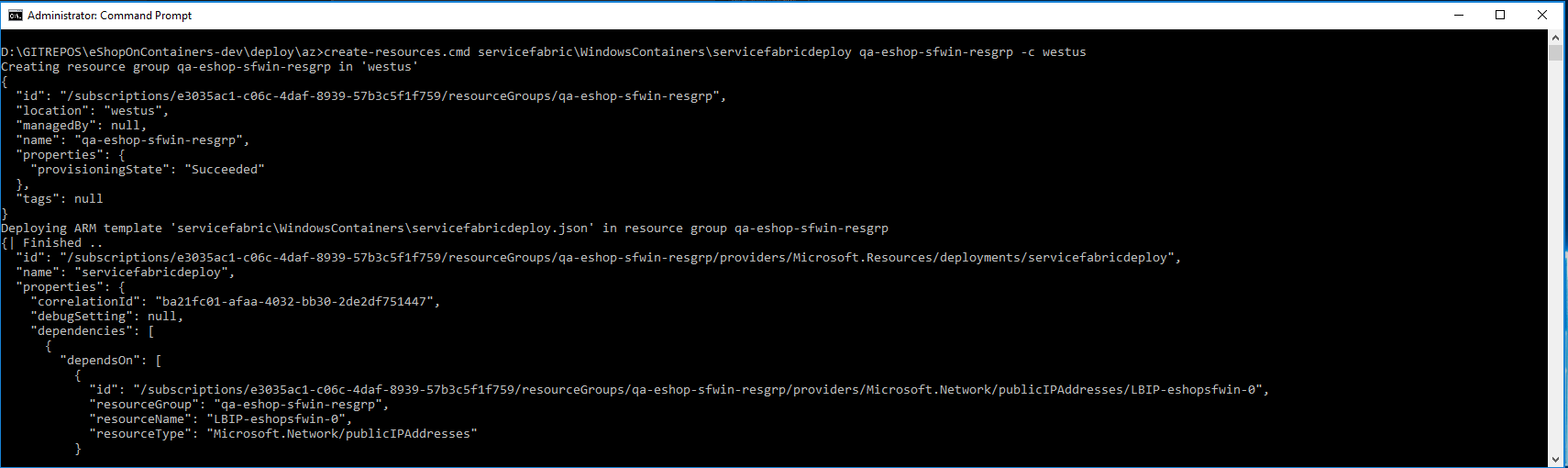
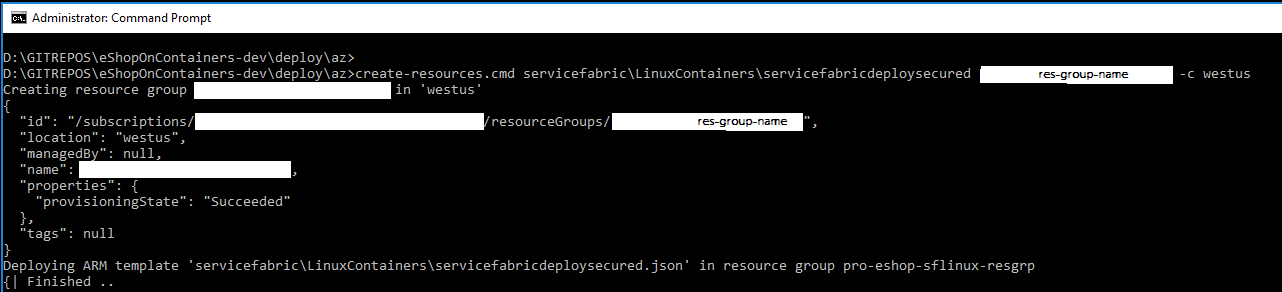
+You should see a similar execution to the following:
+
-# Deploying Azure Service Fabric (Secured)
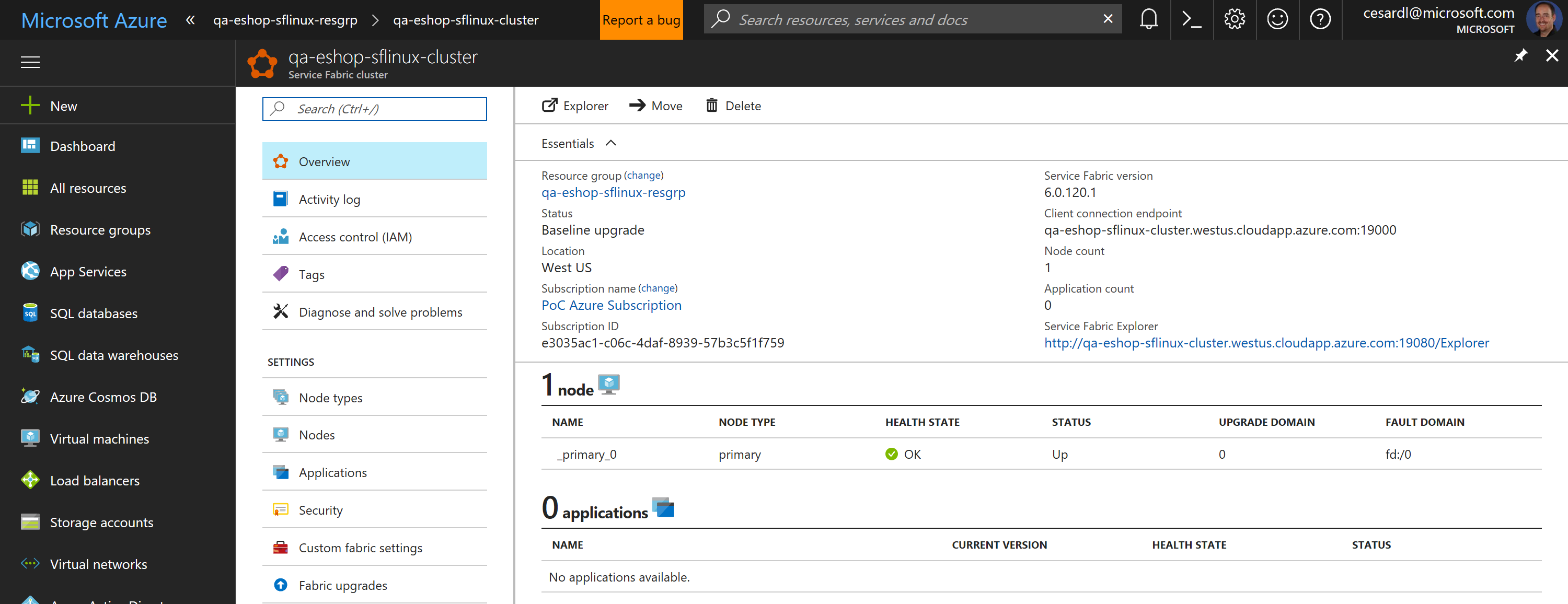
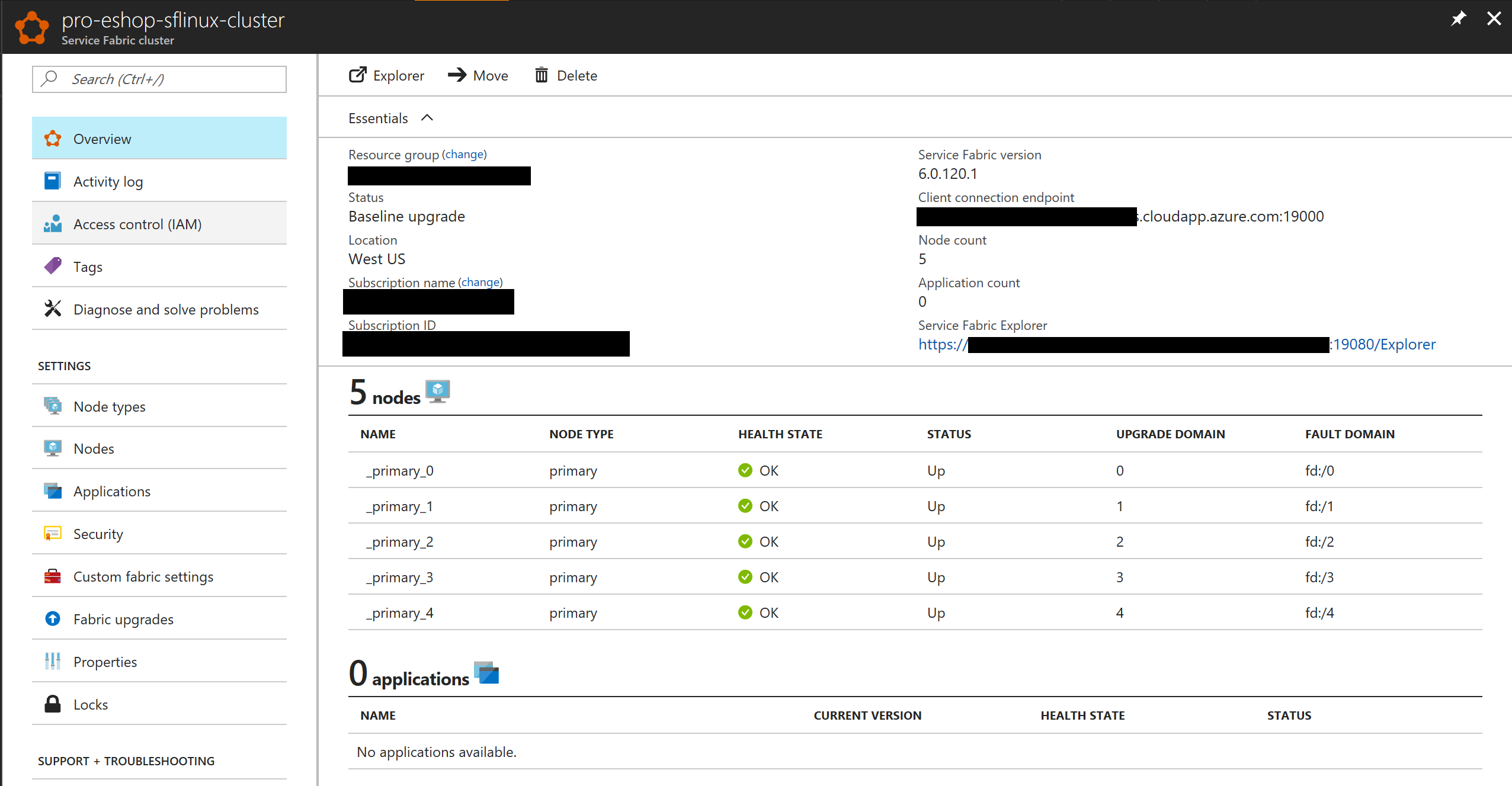
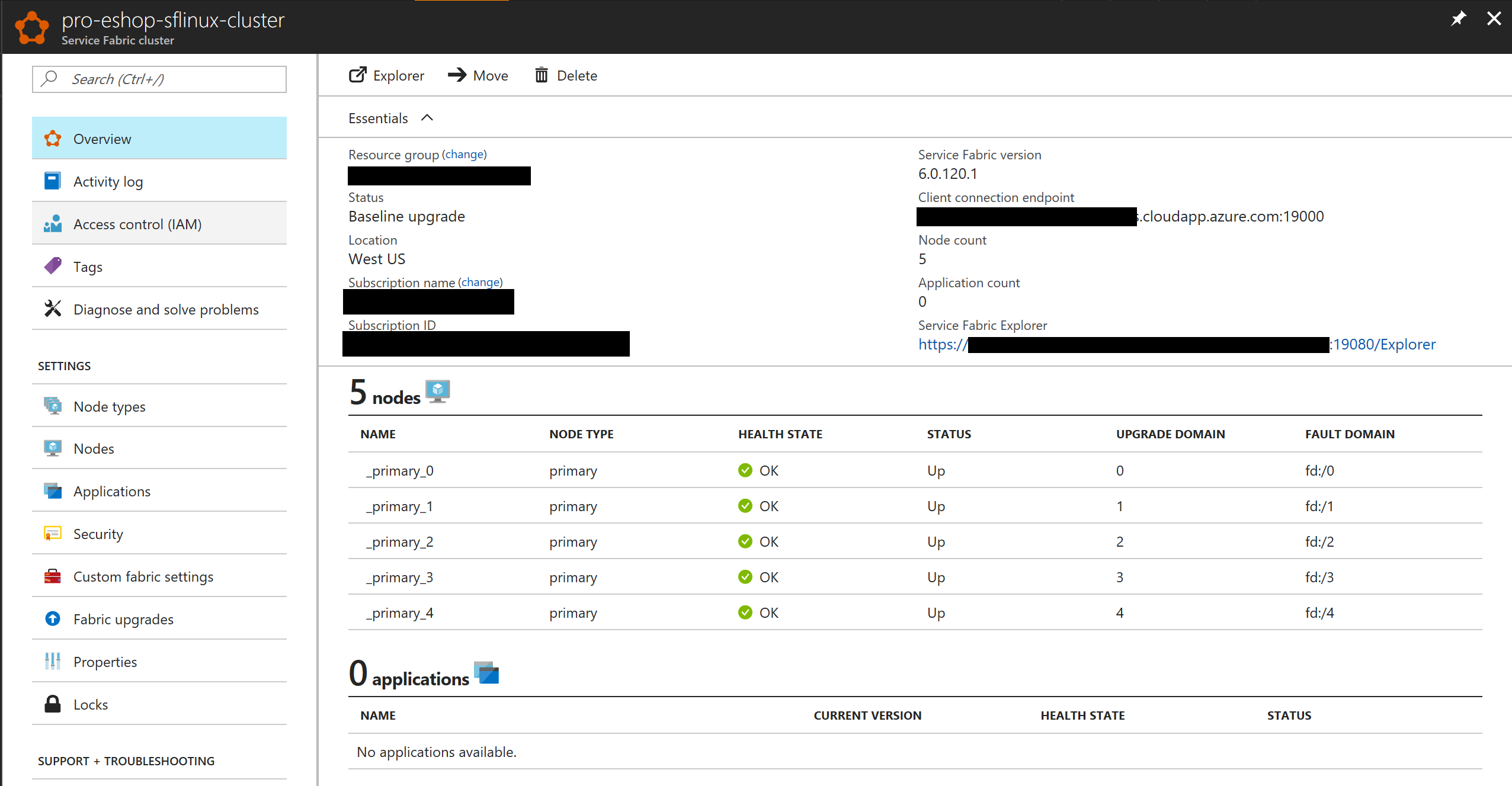
+Now, if you go to your subscription in Azure, you should be able to see the SF cluster already created and available, like in the following image:
+
+
+
+In this case, this is an unsecured SF cluster with a single Linux node, good for initial tests and getting started with SF.
+
+## B. Secured cluster (SF Linux cluster)
+
+Within eShopOnContainers root folder, at the folder [..\deploy\az\servicefabric\LinuxContainers](https://github.com/dotnet-architecture/eShopOnContainers/tree/dev/deploy/az/servicefabric/LinuxContainers), you can find the ARM template `servicefabricdeploysecured.json` and its parameter file (`servicefabricdeploysecured.parameters.json`) to create a secured Service Fabric cluster environment for Linux Containers (IN THIS CASE, IT IS A SECURED CLUSTER USING A CERTIFICATE).
The ARM template `servicefabricdeploysecured.json` and its parameter file (`servicefabricdeploysecured.parameters.json`) are used to create a service fabric cluster environment for linux containers secured with a certificate.
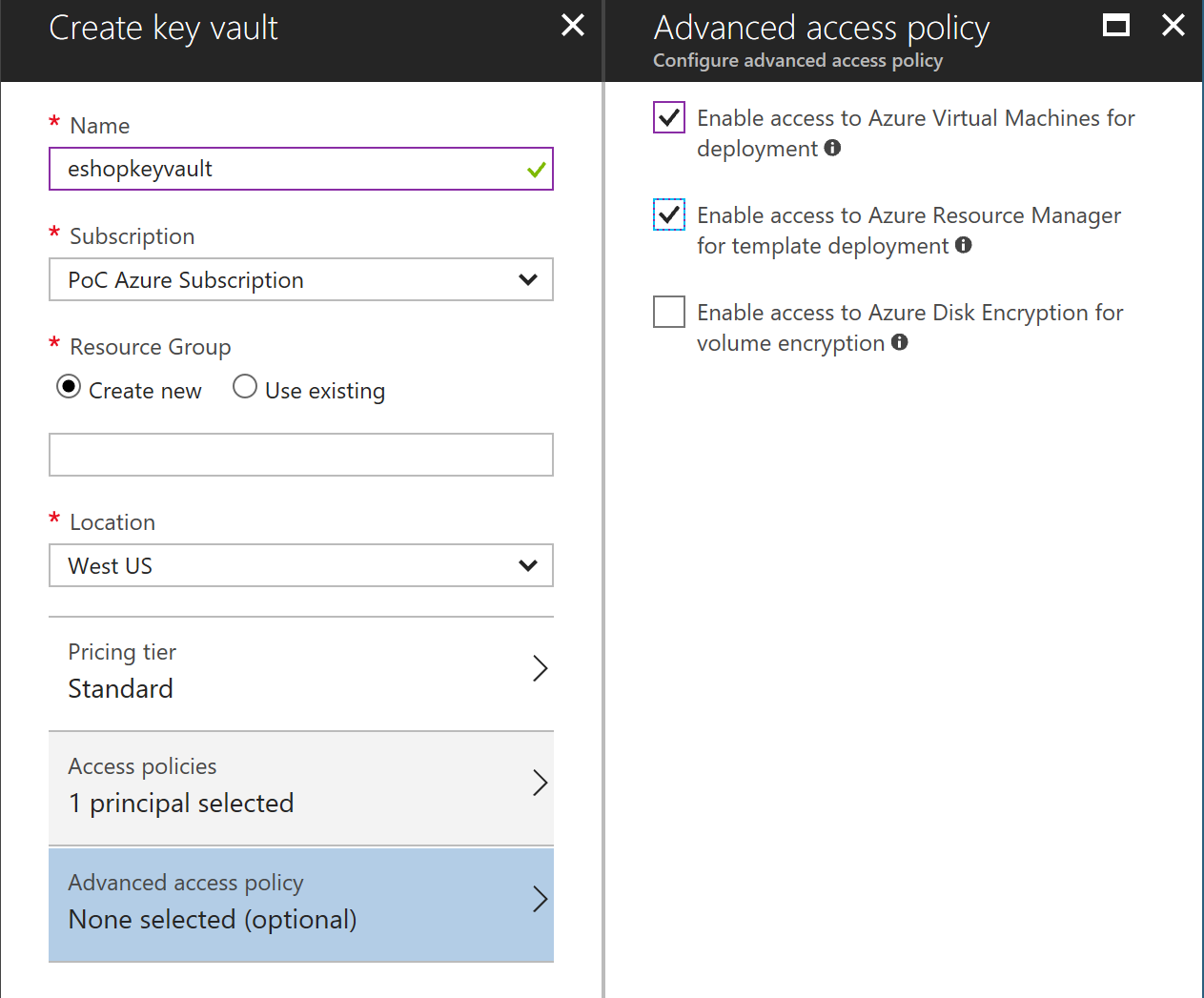
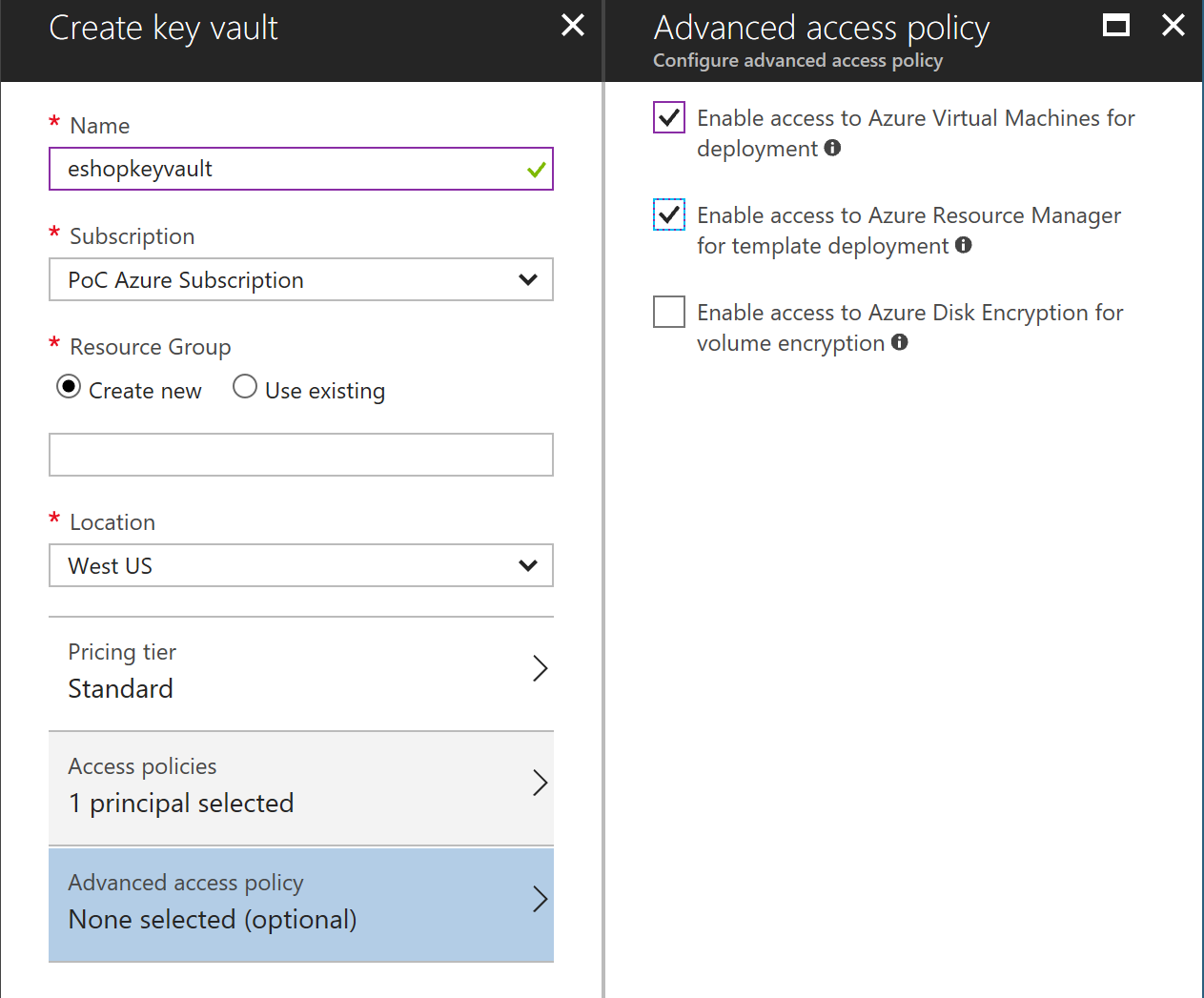
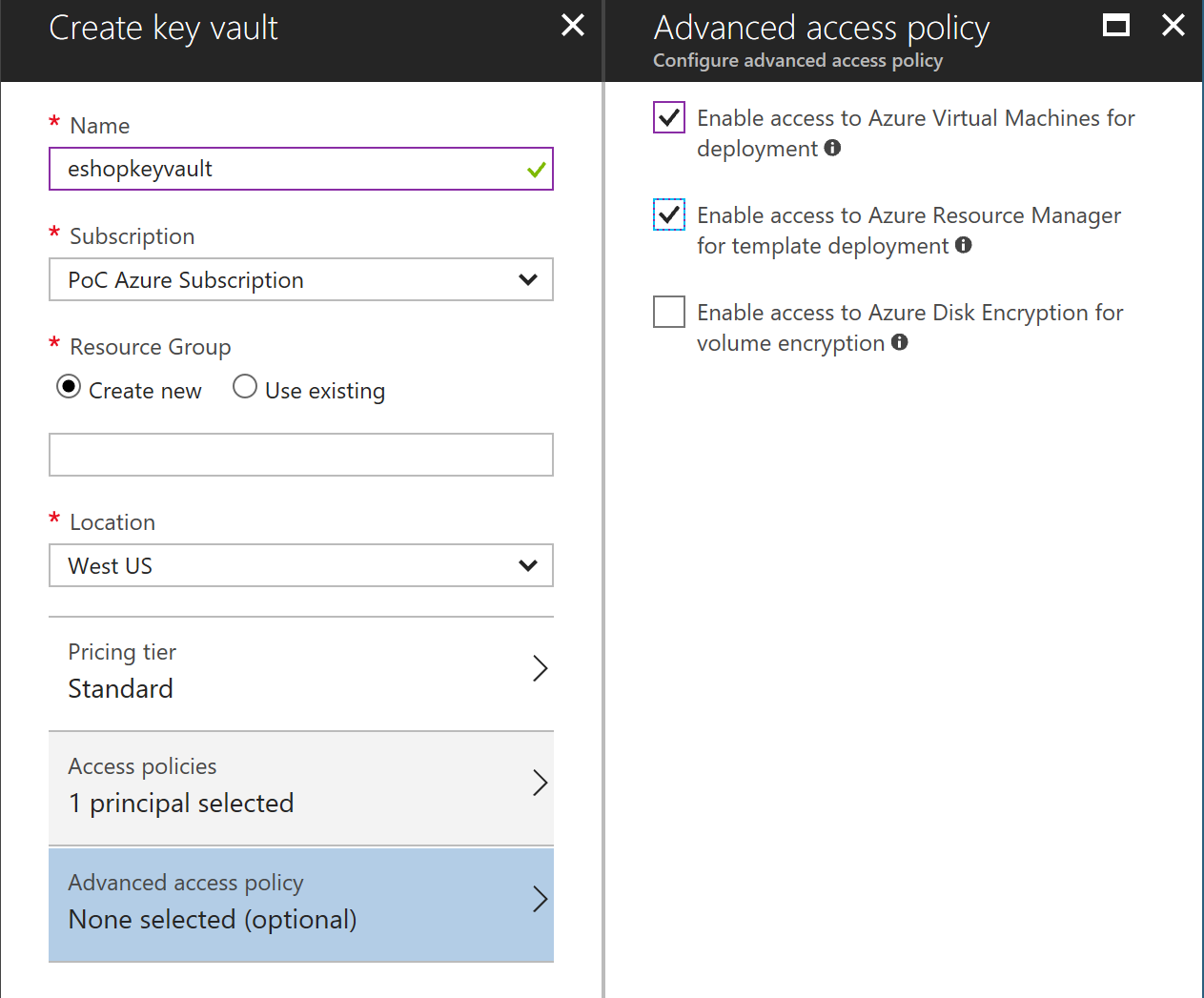
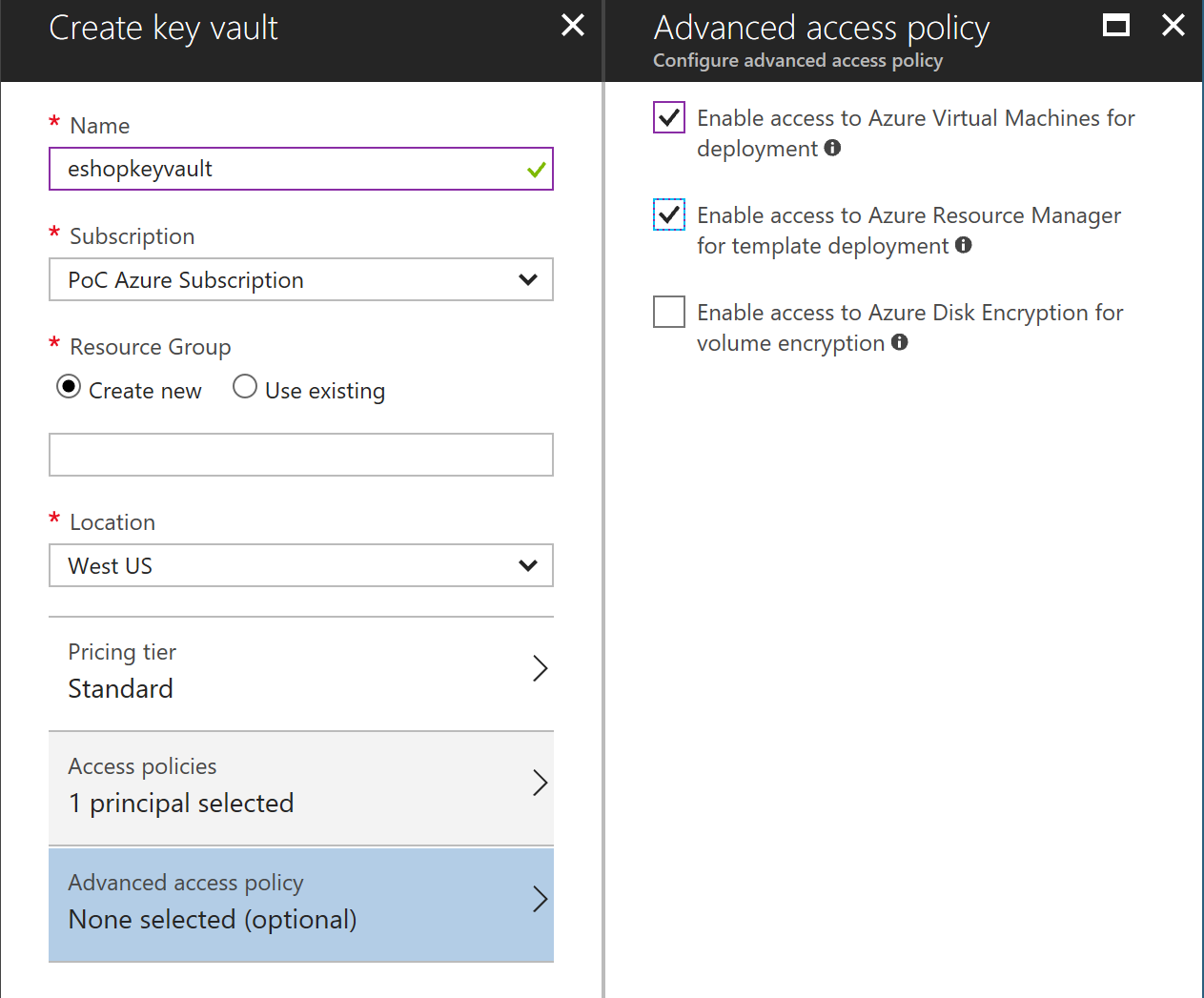
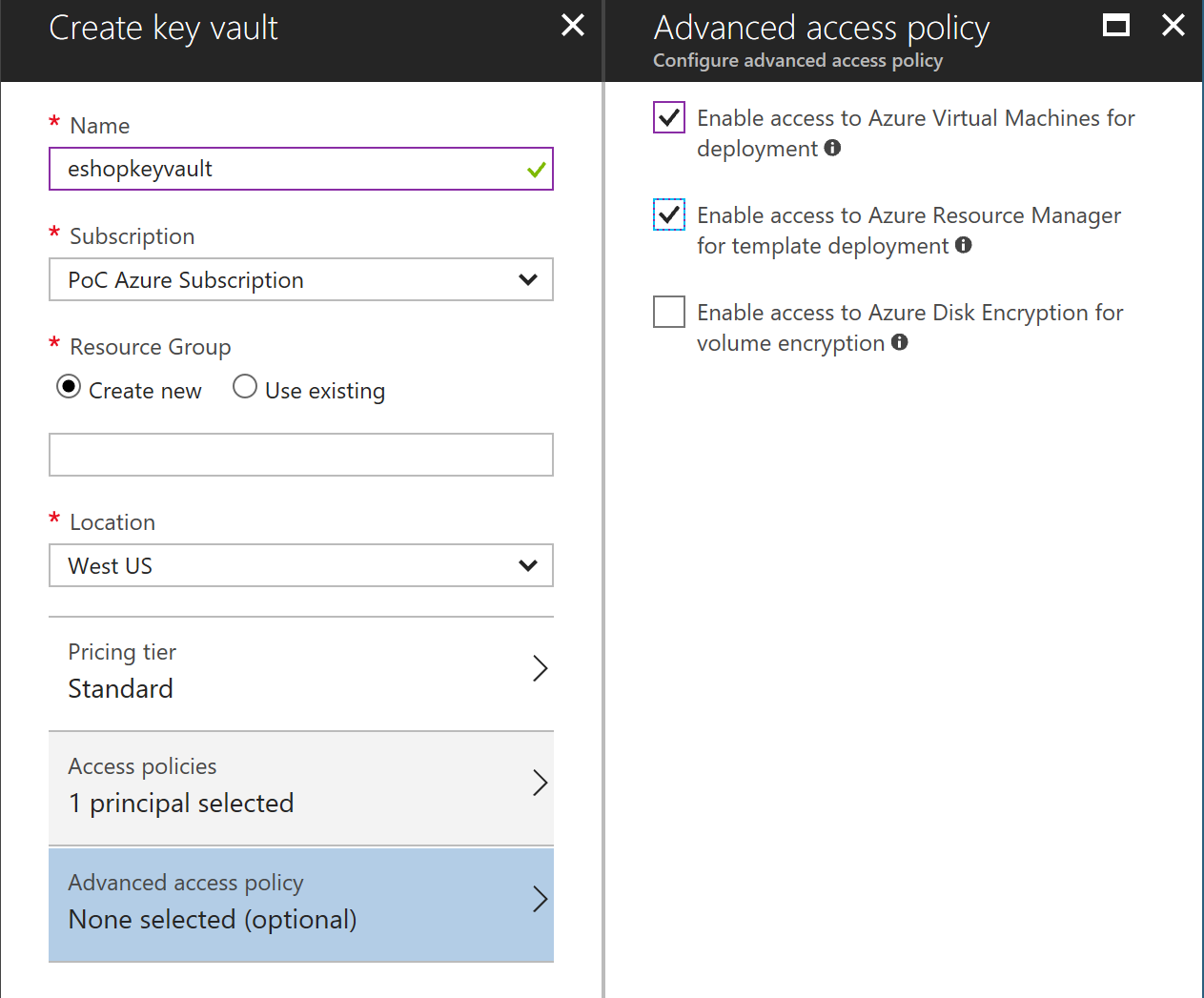
## Create Azure Keyvault service
Go to PortalAzure and create a Keyvault service. Make sure Enable access for deployment checkboxes are selected.
- +
## Generate a certificate in Azure Keyvault
+In a POWER-SHELL window, move to the folder [..\deploy\az\servicefabric\LinuxContainers](https://github.com/dotnet-architecture/eShopOnContainers/tree/dev/deploy/az/servicefabric/LinuxContainers).
+
+**Select your Azure subscription** You might have [several Azure subscriptions](https://docs.microsoft.com/en-us/cli/azure/account#set) as shown if you type the following.
+
+ >```
+ >az account list
+ >```
+ If you have multiple subscription accounts, you first need to select the Azure subscription account you want to target. Type the following:
+ >```
+ >az account set --subscription "Your Azure Subscription Name or ID"
+ >```
+
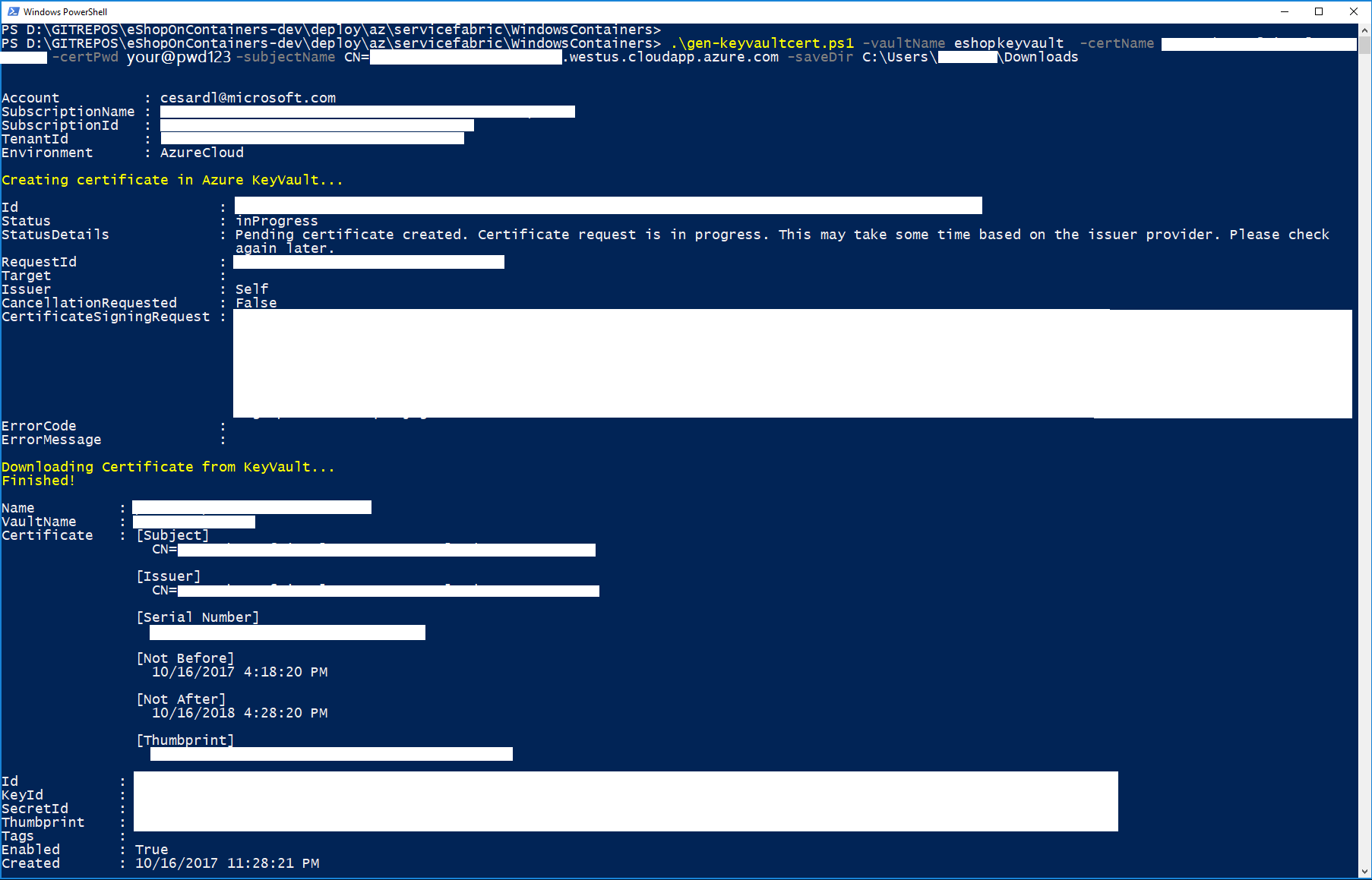
Execute the gen-keyvaultcert.ps1 script to generate and download a certificate from Keyvault.
```
.\gen-keyvaultcert.ps1 -vaultName -certName -certPwd -subjectName CN=.westeurope.cloudapp.azure.com -saveDir C:\Users\\Downloads
```
-## Install the certificate
-Install the certificate under 'Current User' store location and check it as exportable.
-
+
## Generate a certificate in Azure Keyvault
+In a POWER-SHELL window, move to the folder [..\deploy\az\servicefabric\LinuxContainers](https://github.com/dotnet-architecture/eShopOnContainers/tree/dev/deploy/az/servicefabric/LinuxContainers).
+
+**Select your Azure subscription** You might have [several Azure subscriptions](https://docs.microsoft.com/en-us/cli/azure/account#set) as shown if you type the following.
+
+ >```
+ >az account list
+ >```
+ If you have multiple subscription accounts, you first need to select the Azure subscription account you want to target. Type the following:
+ >```
+ >az account set --subscription "Your Azure Subscription Name or ID"
+ >```
+
Execute the gen-keyvaultcert.ps1 script to generate and download a certificate from Keyvault.
```
.\gen-keyvaultcert.ps1 -vaultName -certName -certPwd -subjectName CN=.westeurope.cloudapp.azure.com -saveDir C:\Users\\Downloads
```
-## Install the certificate
-Install the certificate under 'Current User' store location and check it as exportable.
- +You should see a similar execution to the following:
+
+
+IMPORTANT: At this point, copy/cut the .PFX certificate file saved in the downloads forlder and save it in a secure place.
+
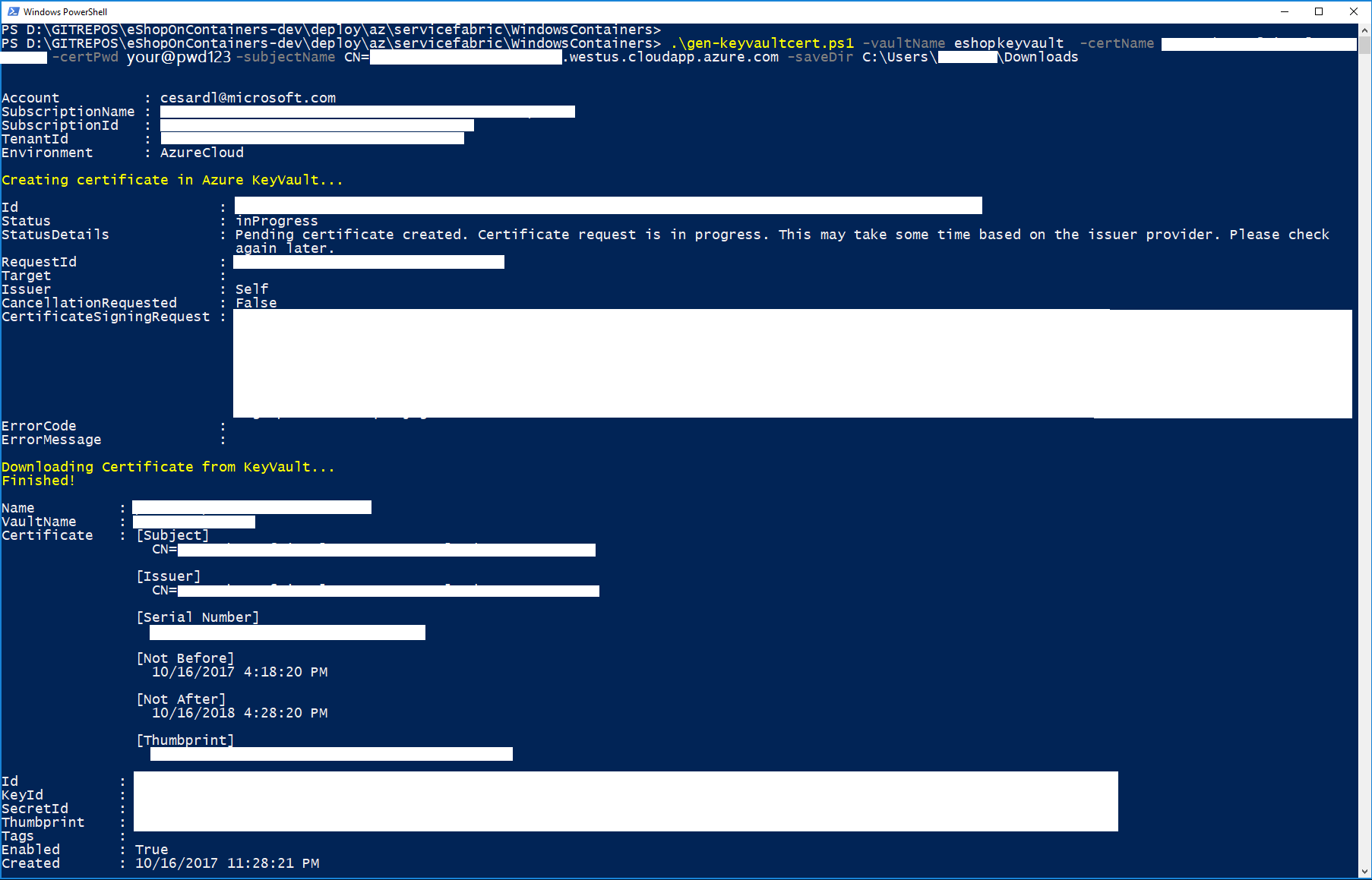
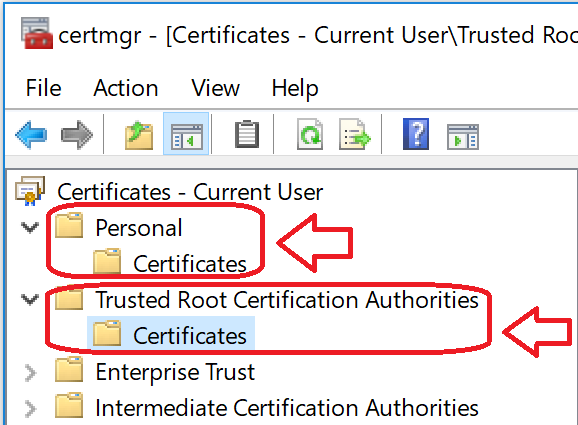
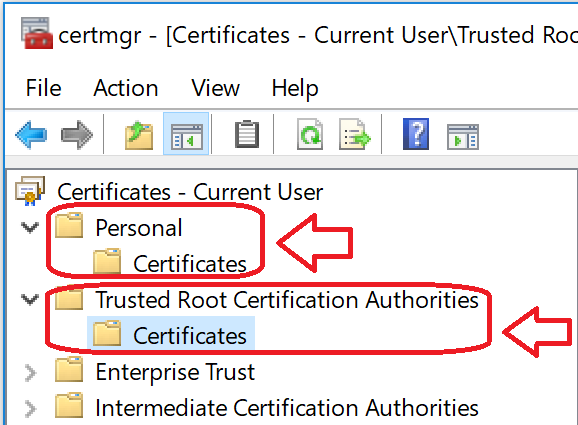
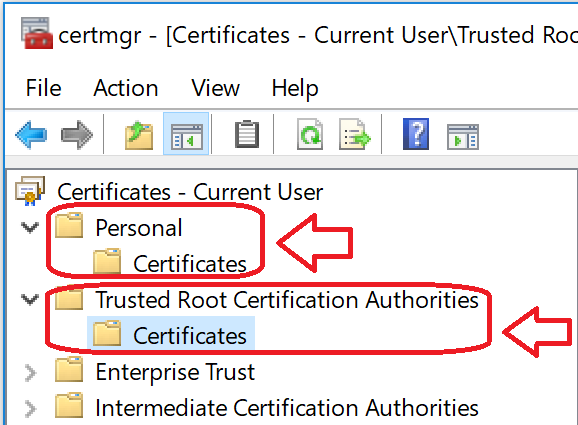
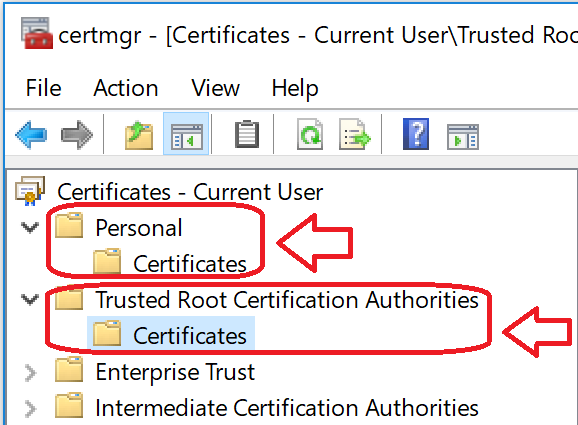
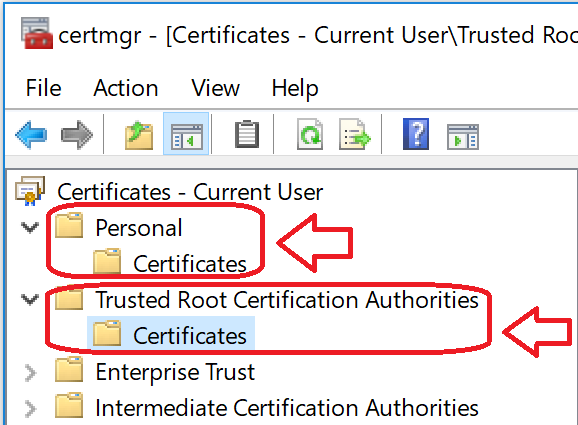
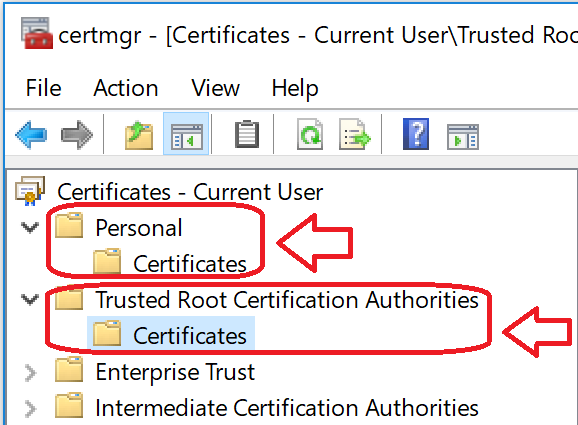
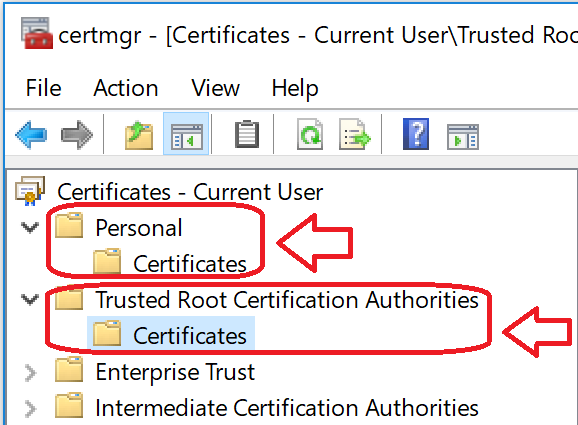
+## Install the certificate
+Install the certificate (by double-clicking on the .PFX file) under 'Current User' store location (by default location) and check it as exportable.
+
+
+You should see a similar execution to the following:
+
+
+IMPORTANT: At this point, copy/cut the .PFX certificate file saved in the downloads forlder and save it in a secure place.
+
+## Install the certificate
+Install the certificate (by double-clicking on the .PFX file) under 'Current User' store location (by default location) and check it as exportable.
+
+ +
+Also, install the same certificate as CA (Certificate Authority) under Current User, too.
+
+
## Editing servicefabricdeploysecured.parameters.json file
-Edit the following params in `servicefabricdeploysecured.parameters.json` file to set your values:
+Edit the parameters in `servicefabricdeploysecured.parameters.json` in a similar way you can do with the unsecured .json file shown above (clusterName, dnsName, etc.), plus edit the following values:
-- clusterName: Name of your SF cluster
-- dnsName: Name assigned to your SF dns
-- adminUserName: user name for administration
-- adminPassword: user password for administration
-- sourceVaultValue: keyvault resource id (check azure keyvault properties)
-- certificateUrlValue: certificate url (check azure Keyvault certificate properties)
-- certificateThumbprint: certificate thumbprint (check azure Keyvault certificate properties)
+- sourceVaultValue: Your Azure Keyvault's RESOURCE ID (check Azure keyvault properties, similar to: /subscriptions/e1234ac1-c09c-3jaf-6767-98b3c5f1f246/resourceGroups/eshop-global-resgrp/providers/Microsoft.KeyVault/vaults/eshopkeyvault")
-Optionally, you can modify which ports are opened in the LoadBalancer for accessing externally to the apps:
+- certificateUrlValue: Your certificate Secret Identifier (check Azure Keyvault secret certificate properties, should be in the format of https://.vault.azure.net:443/secrets/, similar to:
+https://eshopkeyvault.vault.azure.net/secrets/pro-eshop-sflinux-cluster-cert/fd47684442c04cdj83b3hfe4h8e08123)
-- webMvcHttpPort: port externally exposed for the WebMVC app
-- webSpaHttpPort: port externally exposed for the WebSPA app
-- webStatusHttpPort: port externally exposed for the WebStatus app
-- IdSrvHttpRule: port externally exposed for the Identity app
+- certificateThumbprint: certificate thumbprint (check azure Keyvault certificate thumbprint, something like 69JK453486D55A6818577Z0699100365HDK70FCE)
-## Deploy the template
+## Deploy the secured SF Linux cluster
-Once parameter file is edited you can deploy it using [create-resources script](../readme.md).
+Once parameters file is edited you can deploy it using [create-resources script](../readme.md).
+Use a command prompt window positioned into the deploy\az folder.
```
-create-resources.cmd servicefabric\LinuxContainers\servicefabricdeploysecured newResourceGroup -c westus
+create-resources.cmd servicefabric\LinuxContainers\servicefabricdeploysecured pro-eshop-sflinux-resgrp -c westus
```
+The execution should be something like the following:
+
+
+Once the cluster is created you can explore it with Azure's portal, like in the following image:
+
+
+
## Deploy eShopOnServiceFabric with Visual Studio.
Modify the cloud.xml file of each Service Fabric application in PublishProfile directory and set your certificate settings to be able to deploy eshopOnContainers in the secured cluster:
diff --git a/deploy/az/servicefabric/LinuxContainers/servicefabricdeploy.parameters.json b/deploy/az/servicefabric/LinuxContainers/servicefabricdeploy.parameters.json
index d905f2d00..0e37d24ec 100644
--- a/deploy/az/servicefabric/LinuxContainers/servicefabricdeploy.parameters.json
+++ b/deploy/az/servicefabric/LinuxContainers/servicefabricdeploy.parameters.json
@@ -3,19 +3,19 @@
"contentVersion": "1.0.0.0",
"parameters": {
"clusterName": {
- "value": "your_sf_name"
+ "value": "qa-eshop-sflinux-cluster"
},
"clusterLocation": {
- "value": "westeurope"
+ "value": "westus"
},
"computeLocation": {
- "value": "westeurope"
+ "value": "westus"
},
"adminUserName": {
"value": "eshop"
},
"adminPassword": {
- "value": "your_admin_password"
+ "value": "Your_complex_Pass@word1"
},
"nicName": {
"value": "NIC-eshoponsflin"
@@ -24,7 +24,7 @@
"value": "eshoponsflin-PubIP"
},
"dnsName": {
- "value": "your_sf_dns"
+ "value": "qa-eshop-sflinux-cluster"
},
"virtualNetworkName": {
"value": "VNet-eshoponsflin"
diff --git a/deploy/az/servicefabric/LinuxContainers/servicefabricdeploysecured.parameters.json b/deploy/az/servicefabric/LinuxContainers/servicefabricdeploysecured.parameters.json
index 4a783768e..65875cb31 100644
--- a/deploy/az/servicefabric/LinuxContainers/servicefabricdeploysecured.parameters.json
+++ b/deploy/az/servicefabric/LinuxContainers/servicefabricdeploysecured.parameters.json
@@ -3,19 +3,19 @@
"contentVersion": "1.0.0.0",
"parameters": {
"clusterName": {
- "value": "your_sf_name"
+ "value": "pro-eshop-sflinux-cluster"
},
"clusterLocation": {
- "value": "westeurope"
+ "value": "westus"
},
"computeLocation": {
- "value": "westeurope"
+ "value": "westus"
},
"adminUserName": {
"value": "eshop"
},
"adminPassword": {
- "value": "your_admin_password"
+ "value": "Pass@word1"
},
"nicName": {
"value": "NIC-eshopsflinsec"
@@ -24,25 +24,25 @@
"value": "eshopsflinsec-PubIP"
},
"dnsName": {
- "value": "your_sf_dns"
+ "value": "pro-eshop-sflinux-cluster"
},
"virtualNetworkName": {
- "value": "VNet-eshopsflinsec"
+ "value": "VNet-eshopsflin"
},
"lbName": {
- "value": "LB-eshopsflinsec"
+ "value": "LB-eshopsflin"
},
"lbIPName": {
- "value": "LBIP-eshopsflinsec"
+ "value": "LBIP-eshopsflin"
},
"sourceVaultValue": {
- "value": ""
+ "value": "your-value-check-keyvault-at-azure"
},
"certificateUrlValue": {
- "value": ""
+ "value": "your-value-check-keyvault-at-azure"
},
"certificateThumbprint": {
- "value": ""
+ "value": "your-value-check-keyvault-at-azure"
},
"vmImageSku": {
"value": "16.04-LTS"
diff --git a/deploy/az/servicefabric/WindowsContainers/readme.md b/deploy/az/servicefabric/WindowsContainers/readme.md
index 4b6920e42..18aa8ad78 100644
--- a/deploy/az/servicefabric/WindowsContainers/readme.md
+++ b/deploy/az/servicefabric/WindowsContainers/readme.md
@@ -1,84 +1,134 @@
-# Deploying Azure Service Fabric (No Secured)
+# Deploying a Service Fabric cluster based on Windows nodes
-The ARM template `servicefabricdeploy.json` and its parameter file (`servicefabricdeploy.parameters.json`) are used to create a service fabric cluster environment for windows containers.
+## A. Unsecured cluster (SF Windows cluster)
+For a secured cluster, see option B. below.
-## Editing servicefabricdeploy.parameters.json file
+You can always deploy a SF cluster through the Azure portal, as explained in this article: https://docs.microsoft.com/en-us/azure/service-fabric/service-fabric-get-started-azure-cluster
+
+However, when creating a cluster, there are quite a few configurations to take into account, like enabling the internal DNS service or Reverse Proxy service, choosing between Linux/Windows, open/publish your application ports in the load-balancer and most of all (the most complex setup) how to create a secure cluster.
+
+Because of those reasons, we have created a set of ARM templates and scripts so you can create, re-create and configure the SF clusters much faster, as explained below:
+
+Within eShopOnContainers root folder, at the folder [..\deploy\az\servicefabric\WindowsContainers](https://github.com/dotnet-architecture/eShopOnContainers/tree/dev/deploy/az/servicefabric/WindowsContainers), you can find the ARM template `servicefabricdeploy.json` and its parameters file (`servicefabricdeploy.parameters.json`) to create a Service Fabric cluster environment for Windows Containers (NOT SECURED CLUSTER).
+
+## Edit the servicefabricdeploy.parameters.json file
Edit the following params in `servicefabricdeploy.parameters.json` file to set your values:
- clusterName: Name of your SF cluster
+- clusterLocation: Datacenter location, like westus or westeurope
+- computeLocation: Datacenter location, like westus or westeurope
+- adminUserName: user-name for VMs administration
+- adminPassword: user-password for VMs administration
- dnsName: Name assigned to your SF dns
-- adminUserName: user name for administration
-- adminPassword: user password for administration
-Optionally, you can modify which ports are opened in the LoadBalancer for accessing externally to the apps:
+Optionally, you could modify which ports are opened in the LoadBalancer for the multiple eShopOnContainer apps and API services.
+By default, they are setup as:
+- webMvcHttpPort: 5100
+- webSpaHttpPort: 5104
+- webStatusHttpPort: 5107
+- IdSrvHttpRule: 5105
+- BasketApiHttpRule: 5103
+- CatalogApiHttpRule: 5101
+- OrderingApiHttpRule: 5102
+- MarketingApiHttpRule: 5110
+- LocationsApiHttpRule: 5109
-- webMvcHttpPort: port externally exposed for the WebMVC app
-- webSpaHttpPort: port externally exposed for the WebSPA app
-- webStatusHttpPort: port externally exposed for the WebStatus app
-- IdSrvHttpRule: port externally exposed for the Identity app
-
-## Deploy the template
+## Deploy the Service Fabric cluster using the script and ARM templates
Once parameter file is edited you can deploy it using [create-resources script](../readme.md).
-i. e. if you are in windows, to deploy sql databases in a new resourcegroup located in westus, go to `deploy\az` folder and type:
-
+For example, to deploy the cluster to a new resourcegroup located in westus, using the Command Prompt, go to `deploy\az` folder and type:
```
-create-resources.cmd servicefabric\WindowsContainers\servicefabricdeploy newResourceGroup -c westus
+create-resources.cmd servicefabric\WindowsContainers\servicefabricdeploy qa-eshop-sfwin-resgrp -c westus
```
-## Deploy eShopOnServiceFabric with Visual Studio.
-Alternatively, instead of using ARM templates, you can deploy eShop on service fabric directly by publishing the project eShopOnServiceFabric in eShopOnContainers-ServicesAndWebApps.sln with Visual Studio publish tool.
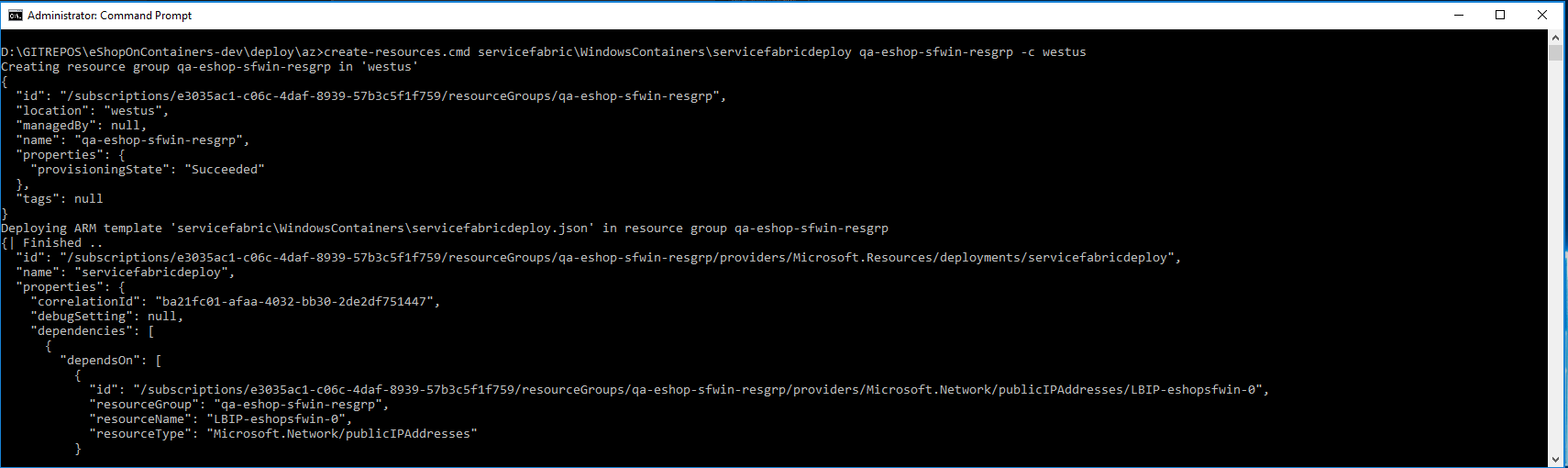
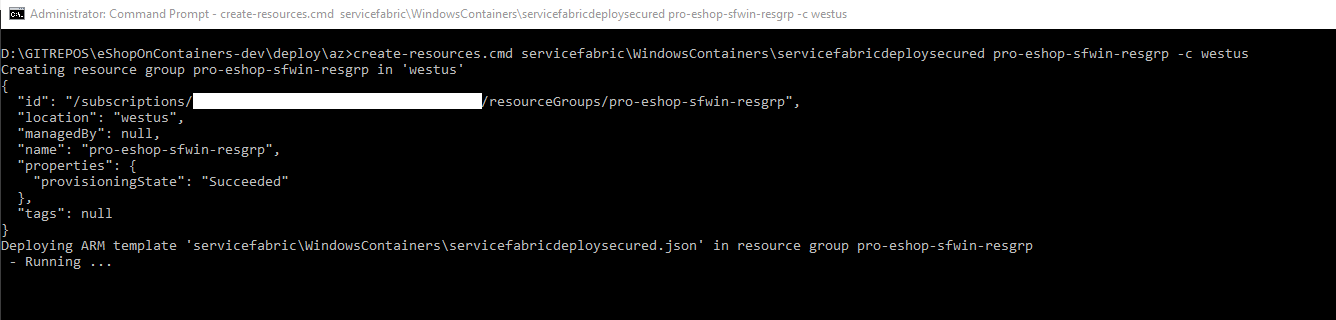
+You should see a similar execution to the following:
+
-# Deploying Azure Service Fabric (Secured)
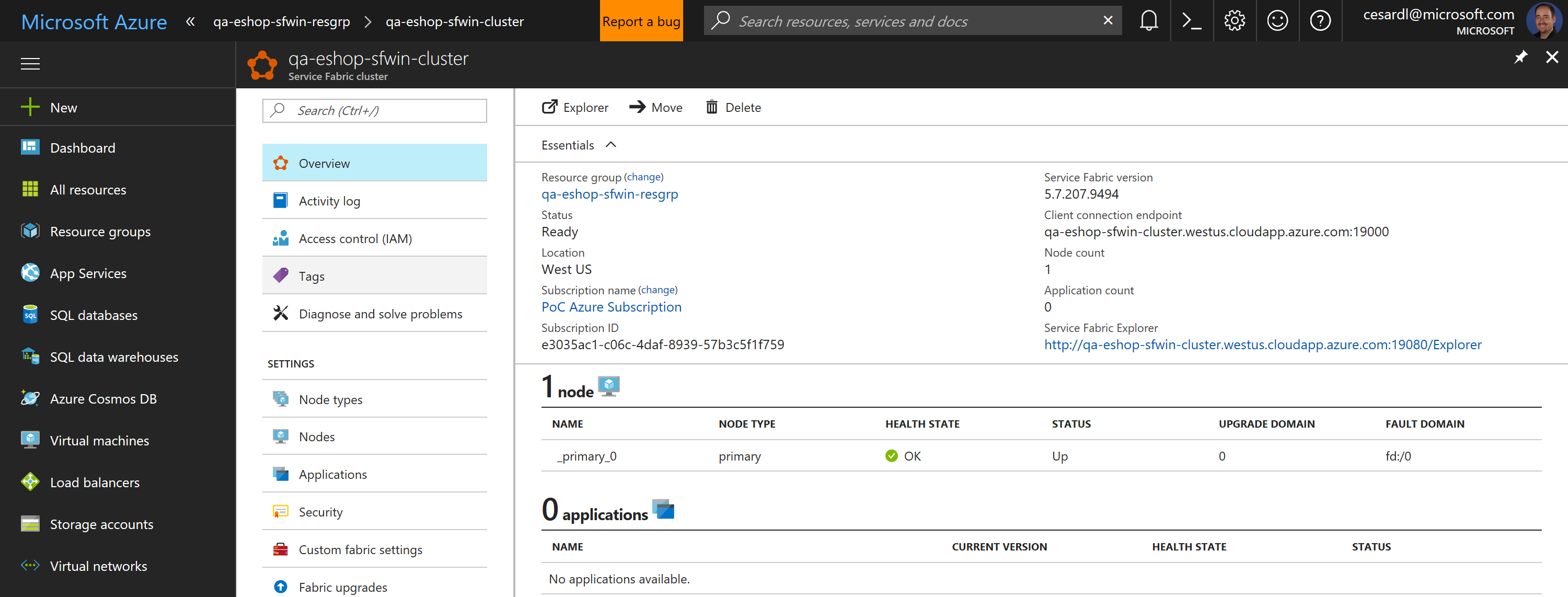
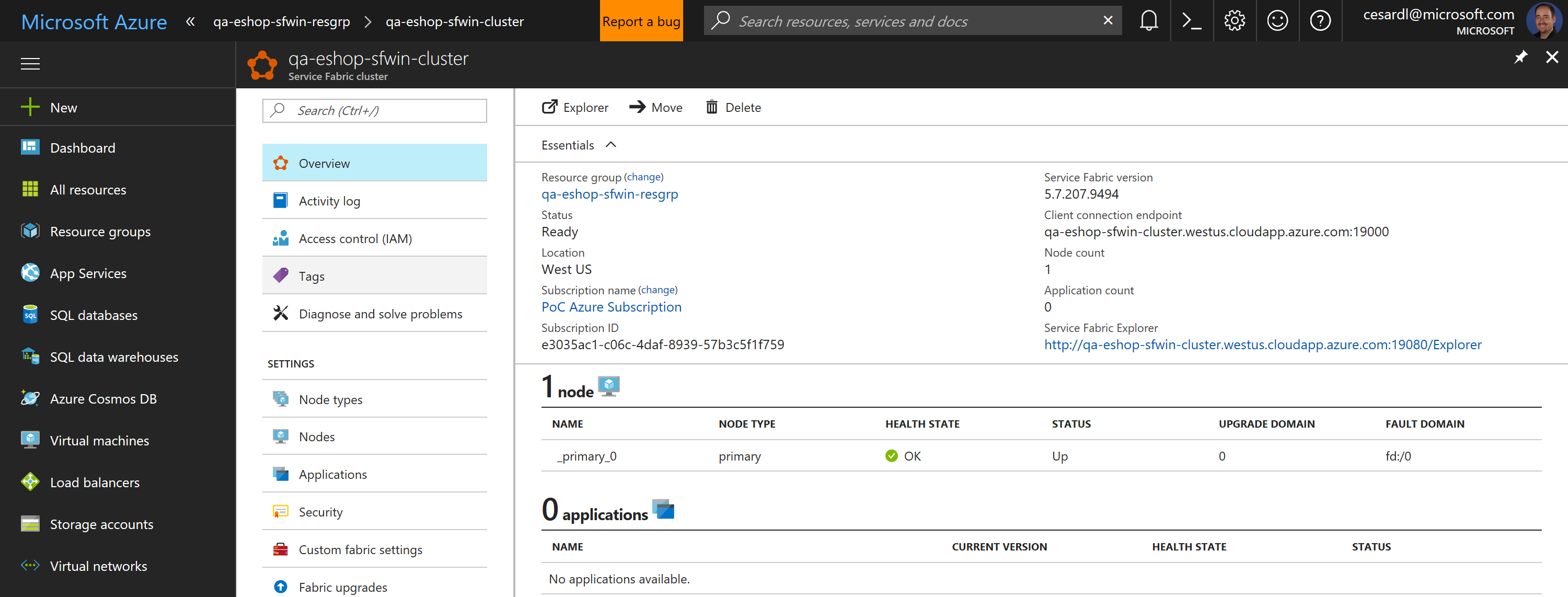
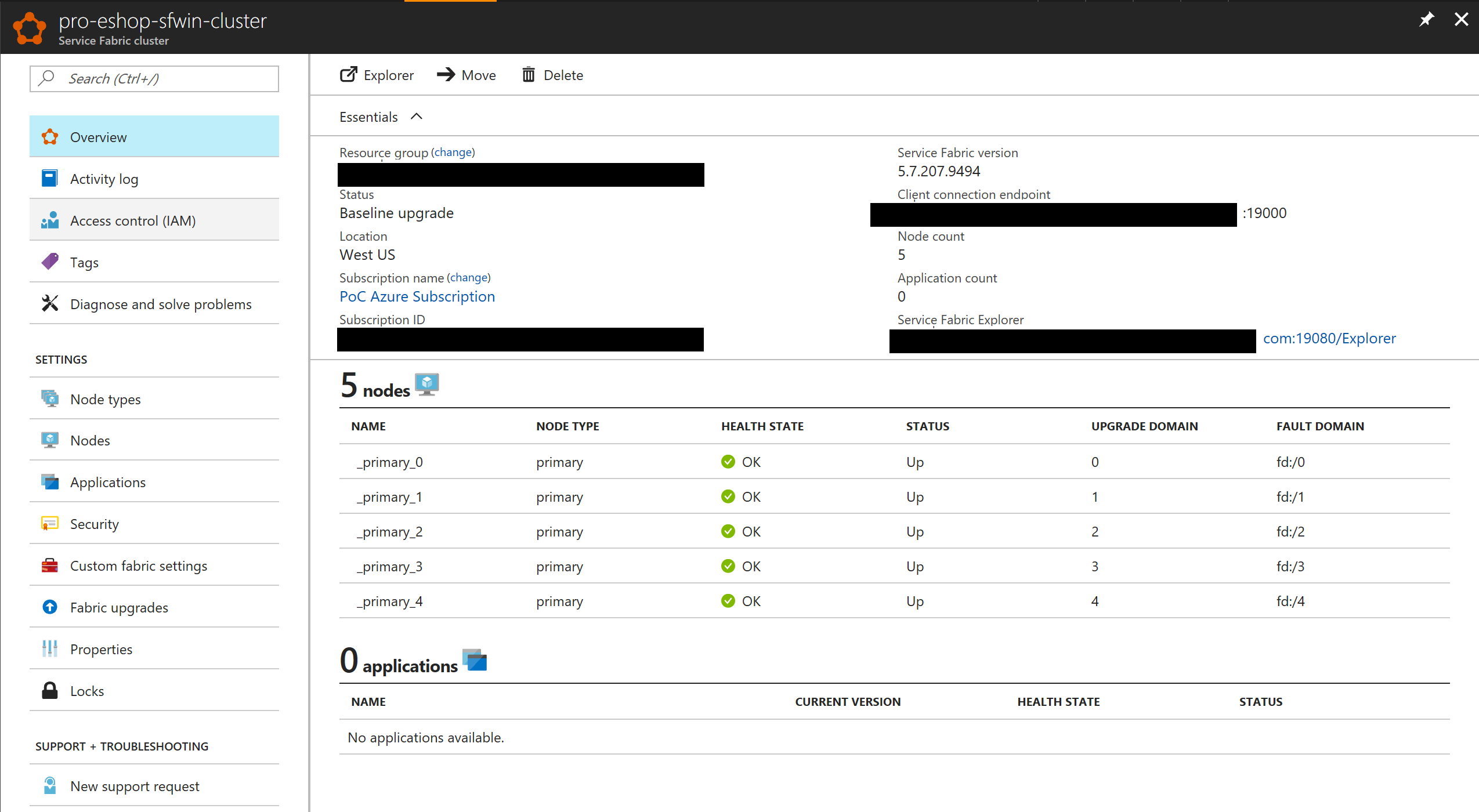
+Now, if you go to your subscription in Azure, you should be able to see the SF cluster already created and available, like in the following image:
-The ARM template `servicefabricdeploysecured.json` and its parameter file (`servicefabricdeploysecured.parameters.json`) are used to create a service fabric cluster environment for windows containers secured with a certificate.
+
+
+In this case, this is an unsecured SF cluster with a single Windows node, good for initial tests and getting started with SF.
+
+
+## B. Secured cluster (SF Windows cluster)
+
+Within eShopOnContainers root folder, at the folder [..\deploy\az\servicefabric\WindowsContainers](https://github.com/dotnet-architecture/eShopOnContainers/tree/dev/deploy/az/servicefabric/WindowsContainers), you can find the ARM template `servicefabricdeploysecured.json` and its parameter file (`servicefabricdeploysecured.parameters.json`) to create a secured Service Fabric cluster environment for Windows Containers (IN THIS CASE, IT IS A SECURED CLUSTER USING A CERTIFICATE).
## Create Azure Keyvault service
Go to PortalAzure and create a Keyvault service. Make sure Enable access for deployment checkboxes are selected.
-
+
+Also, install the same certificate as CA (Certificate Authority) under Current User, too.
+
+
## Editing servicefabricdeploysecured.parameters.json file
-Edit the following params in `servicefabricdeploysecured.parameters.json` file to set your values:
+Edit the parameters in `servicefabricdeploysecured.parameters.json` in a similar way you can do with the unsecured .json file shown above (clusterName, dnsName, etc.), plus edit the following values:
-- clusterName: Name of your SF cluster
-- dnsName: Name assigned to your SF dns
-- adminUserName: user name for administration
-- adminPassword: user password for administration
-- sourceVaultValue: keyvault resource id (check azure keyvault properties)
-- certificateUrlValue: certificate url (check azure Keyvault certificate properties)
-- certificateThumbprint: certificate thumbprint (check azure Keyvault certificate properties)
+- sourceVaultValue: Your Azure Keyvault's RESOURCE ID (check Azure keyvault properties, similar to: /subscriptions/e1234ac1-c09c-3jaf-6767-98b3c5f1f246/resourceGroups/eshop-global-resgrp/providers/Microsoft.KeyVault/vaults/eshopkeyvault")
-Optionally, you can modify which ports are opened in the LoadBalancer for accessing externally to the apps:
+- certificateUrlValue: Your certificate Secret Identifier (check Azure Keyvault secret certificate properties, should be in the format of https://.vault.azure.net:443/secrets/, similar to:
+https://eshopkeyvault.vault.azure.net/secrets/pro-eshop-sflinux-cluster-cert/fd47684442c04cdj83b3hfe4h8e08123)
-- webMvcHttpPort: port externally exposed for the WebMVC app
-- webSpaHttpPort: port externally exposed for the WebSPA app
-- webStatusHttpPort: port externally exposed for the WebStatus app
-- IdSrvHttpRule: port externally exposed for the Identity app
+- certificateThumbprint: certificate thumbprint (check azure Keyvault certificate thumbprint, something like 69JK453486D55A6818577Z0699100365HDK70FCE)
-## Deploy the template
+## Deploy the secured SF Linux cluster
-Once parameter file is edited you can deploy it using [create-resources script](../readme.md).
+Once parameters file is edited you can deploy it using [create-resources script](../readme.md).
+Use a command prompt window positioned into the deploy\az folder.
```
-create-resources.cmd servicefabric\LinuxContainers\servicefabricdeploysecured newResourceGroup -c westus
+create-resources.cmd servicefabric\LinuxContainers\servicefabricdeploysecured pro-eshop-sflinux-resgrp -c westus
```
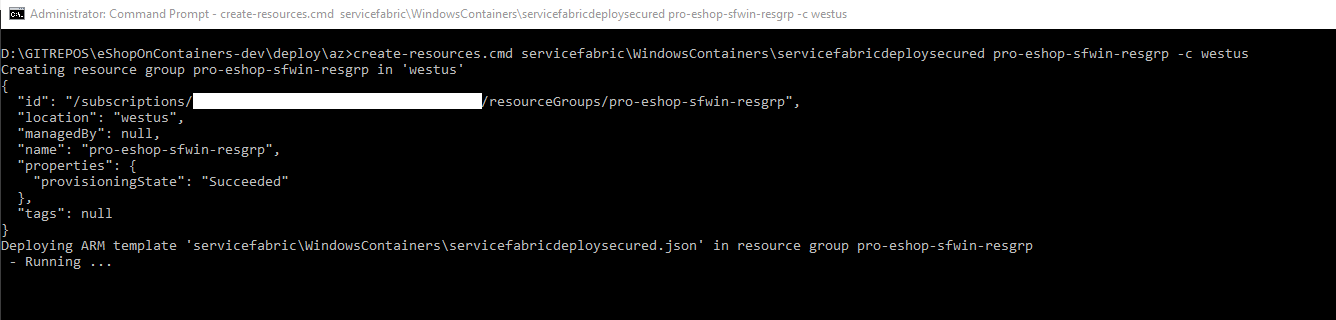
+The execution should be something like the following:
+
+
+Once the cluster is created you can explore it with Azure's portal, like in the following image:
+
+
+
## Deploy eShopOnServiceFabric with Visual Studio.
Modify the cloud.xml file of each Service Fabric application in PublishProfile directory and set your certificate settings to be able to deploy eshopOnContainers in the secured cluster:
diff --git a/deploy/az/servicefabric/LinuxContainers/servicefabricdeploy.parameters.json b/deploy/az/servicefabric/LinuxContainers/servicefabricdeploy.parameters.json
index d905f2d00..0e37d24ec 100644
--- a/deploy/az/servicefabric/LinuxContainers/servicefabricdeploy.parameters.json
+++ b/deploy/az/servicefabric/LinuxContainers/servicefabricdeploy.parameters.json
@@ -3,19 +3,19 @@
"contentVersion": "1.0.0.0",
"parameters": {
"clusterName": {
- "value": "your_sf_name"
+ "value": "qa-eshop-sflinux-cluster"
},
"clusterLocation": {
- "value": "westeurope"
+ "value": "westus"
},
"computeLocation": {
- "value": "westeurope"
+ "value": "westus"
},
"adminUserName": {
"value": "eshop"
},
"adminPassword": {
- "value": "your_admin_password"
+ "value": "Your_complex_Pass@word1"
},
"nicName": {
"value": "NIC-eshoponsflin"
@@ -24,7 +24,7 @@
"value": "eshoponsflin-PubIP"
},
"dnsName": {
- "value": "your_sf_dns"
+ "value": "qa-eshop-sflinux-cluster"
},
"virtualNetworkName": {
"value": "VNet-eshoponsflin"
diff --git a/deploy/az/servicefabric/LinuxContainers/servicefabricdeploysecured.parameters.json b/deploy/az/servicefabric/LinuxContainers/servicefabricdeploysecured.parameters.json
index 4a783768e..65875cb31 100644
--- a/deploy/az/servicefabric/LinuxContainers/servicefabricdeploysecured.parameters.json
+++ b/deploy/az/servicefabric/LinuxContainers/servicefabricdeploysecured.parameters.json
@@ -3,19 +3,19 @@
"contentVersion": "1.0.0.0",
"parameters": {
"clusterName": {
- "value": "your_sf_name"
+ "value": "pro-eshop-sflinux-cluster"
},
"clusterLocation": {
- "value": "westeurope"
+ "value": "westus"
},
"computeLocation": {
- "value": "westeurope"
+ "value": "westus"
},
"adminUserName": {
"value": "eshop"
},
"adminPassword": {
- "value": "your_admin_password"
+ "value": "Pass@word1"
},
"nicName": {
"value": "NIC-eshopsflinsec"
@@ -24,25 +24,25 @@
"value": "eshopsflinsec-PubIP"
},
"dnsName": {
- "value": "your_sf_dns"
+ "value": "pro-eshop-sflinux-cluster"
},
"virtualNetworkName": {
- "value": "VNet-eshopsflinsec"
+ "value": "VNet-eshopsflin"
},
"lbName": {
- "value": "LB-eshopsflinsec"
+ "value": "LB-eshopsflin"
},
"lbIPName": {
- "value": "LBIP-eshopsflinsec"
+ "value": "LBIP-eshopsflin"
},
"sourceVaultValue": {
- "value": ""
+ "value": "your-value-check-keyvault-at-azure"
},
"certificateUrlValue": {
- "value": ""
+ "value": "your-value-check-keyvault-at-azure"
},
"certificateThumbprint": {
- "value": ""
+ "value": "your-value-check-keyvault-at-azure"
},
"vmImageSku": {
"value": "16.04-LTS"
diff --git a/deploy/az/servicefabric/WindowsContainers/readme.md b/deploy/az/servicefabric/WindowsContainers/readme.md
index 4b6920e42..18aa8ad78 100644
--- a/deploy/az/servicefabric/WindowsContainers/readme.md
+++ b/deploy/az/servicefabric/WindowsContainers/readme.md
@@ -1,84 +1,134 @@
-# Deploying Azure Service Fabric (No Secured)
+# Deploying a Service Fabric cluster based on Windows nodes
-The ARM template `servicefabricdeploy.json` and its parameter file (`servicefabricdeploy.parameters.json`) are used to create a service fabric cluster environment for windows containers.
+## A. Unsecured cluster (SF Windows cluster)
+For a secured cluster, see option B. below.
-## Editing servicefabricdeploy.parameters.json file
+You can always deploy a SF cluster through the Azure portal, as explained in this article: https://docs.microsoft.com/en-us/azure/service-fabric/service-fabric-get-started-azure-cluster
+
+However, when creating a cluster, there are quite a few configurations to take into account, like enabling the internal DNS service or Reverse Proxy service, choosing between Linux/Windows, open/publish your application ports in the load-balancer and most of all (the most complex setup) how to create a secure cluster.
+
+Because of those reasons, we have created a set of ARM templates and scripts so you can create, re-create and configure the SF clusters much faster, as explained below:
+
+Within eShopOnContainers root folder, at the folder [..\deploy\az\servicefabric\WindowsContainers](https://github.com/dotnet-architecture/eShopOnContainers/tree/dev/deploy/az/servicefabric/WindowsContainers), you can find the ARM template `servicefabricdeploy.json` and its parameters file (`servicefabricdeploy.parameters.json`) to create a Service Fabric cluster environment for Windows Containers (NOT SECURED CLUSTER).
+
+## Edit the servicefabricdeploy.parameters.json file
Edit the following params in `servicefabricdeploy.parameters.json` file to set your values:
- clusterName: Name of your SF cluster
+- clusterLocation: Datacenter location, like westus or westeurope
+- computeLocation: Datacenter location, like westus or westeurope
+- adminUserName: user-name for VMs administration
+- adminPassword: user-password for VMs administration
- dnsName: Name assigned to your SF dns
-- adminUserName: user name for administration
-- adminPassword: user password for administration
-Optionally, you can modify which ports are opened in the LoadBalancer for accessing externally to the apps:
+Optionally, you could modify which ports are opened in the LoadBalancer for the multiple eShopOnContainer apps and API services.
+By default, they are setup as:
+- webMvcHttpPort: 5100
+- webSpaHttpPort: 5104
+- webStatusHttpPort: 5107
+- IdSrvHttpRule: 5105
+- BasketApiHttpRule: 5103
+- CatalogApiHttpRule: 5101
+- OrderingApiHttpRule: 5102
+- MarketingApiHttpRule: 5110
+- LocationsApiHttpRule: 5109
-- webMvcHttpPort: port externally exposed for the WebMVC app
-- webSpaHttpPort: port externally exposed for the WebSPA app
-- webStatusHttpPort: port externally exposed for the WebStatus app
-- IdSrvHttpRule: port externally exposed for the Identity app
-
-## Deploy the template
+## Deploy the Service Fabric cluster using the script and ARM templates
Once parameter file is edited you can deploy it using [create-resources script](../readme.md).
-i. e. if you are in windows, to deploy sql databases in a new resourcegroup located in westus, go to `deploy\az` folder and type:
-
+For example, to deploy the cluster to a new resourcegroup located in westus, using the Command Prompt, go to `deploy\az` folder and type:
```
-create-resources.cmd servicefabric\WindowsContainers\servicefabricdeploy newResourceGroup -c westus
+create-resources.cmd servicefabric\WindowsContainers\servicefabricdeploy qa-eshop-sfwin-resgrp -c westus
```
-## Deploy eShopOnServiceFabric with Visual Studio.
-Alternatively, instead of using ARM templates, you can deploy eShop on service fabric directly by publishing the project eShopOnServiceFabric in eShopOnContainers-ServicesAndWebApps.sln with Visual Studio publish tool.
+You should see a similar execution to the following:
+
-# Deploying Azure Service Fabric (Secured)
+Now, if you go to your subscription in Azure, you should be able to see the SF cluster already created and available, like in the following image:
-The ARM template `servicefabricdeploysecured.json` and its parameter file (`servicefabricdeploysecured.parameters.json`) are used to create a service fabric cluster environment for windows containers secured with a certificate.
+
+
+In this case, this is an unsecured SF cluster with a single Windows node, good for initial tests and getting started with SF.
+
+
+## B. Secured cluster (SF Windows cluster)
+
+Within eShopOnContainers root folder, at the folder [..\deploy\az\servicefabric\WindowsContainers](https://github.com/dotnet-architecture/eShopOnContainers/tree/dev/deploy/az/servicefabric/WindowsContainers), you can find the ARM template `servicefabricdeploysecured.json` and its parameter file (`servicefabricdeploysecured.parameters.json`) to create a secured Service Fabric cluster environment for Windows Containers (IN THIS CASE, IT IS A SECURED CLUSTER USING A CERTIFICATE).
## Create Azure Keyvault service
Go to PortalAzure and create a Keyvault service. Make sure Enable access for deployment checkboxes are selected.
- +
## Generate a certificate in Azure Keyvault
-Execute the gen-keyvaultcert.ps1 script to generate and download a certificate from Keyvault.
+In a POWER-SHELL window, move to the folder [..\deploy\az\servicefabric\WindowsContainers](https://github.com/dotnet-architecture/eShopOnContainers/tree/dev/deploy/az/servicefabric/WindowsContainers).
+
+**Select your Azure subscription** You might have [several Azure subscriptions](https://docs.microsoft.com/en-us/cli/azure/account#set) as shown if you type the following.
+
+ >```
+ >az account list
+ >```
+ If you have multiple subscription accounts, you first need to select the Azure subscription account you want to target. Type the following:
+ >```
+ >az account set --subscription "Your Azure Subscription Name or ID"
+ >```
+
+**Execute the gen-keyvaultcert.ps1 script** to generate and download a certificate from Keyvault.
+Make sure you're going to run it against the Azure subscription you mean it.
+
+You might need to authenticate from the browser when running this PowerShell script.
```
-.\gen-keyvaultcert.ps1 -vaultName -certName -certPwd -subjectName CN=.westeurope.cloudapp.azure.com -saveDir C:\Users\\Downloads
+.\gen-keyvaultcert.ps1 -vaultName -certName -certPwd -subjectName CN=.westus.cloudapp.azure.com -saveDir C:\Users\\Downloads
```
+You should see a similar execution to the following:
+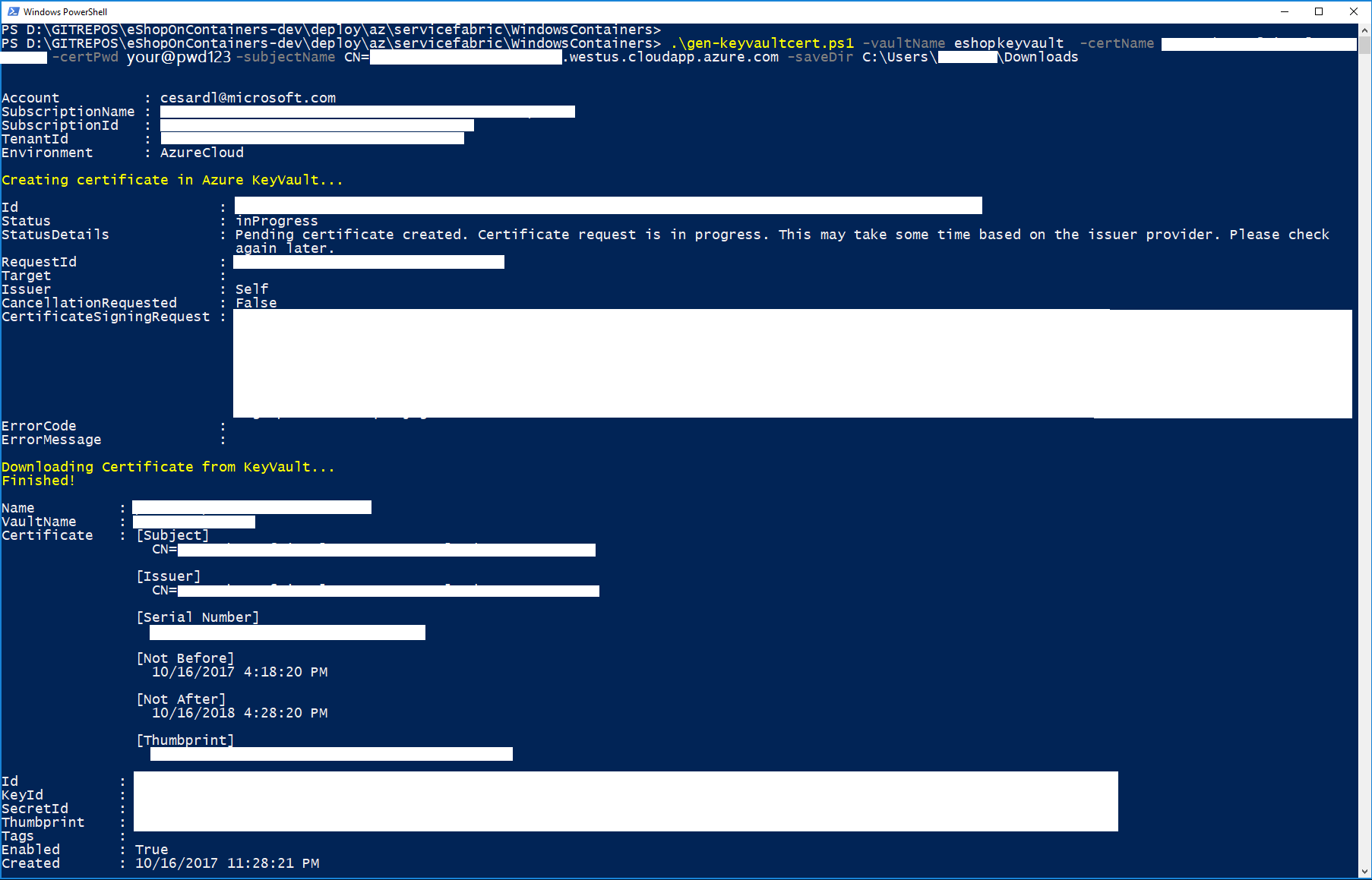
+
+IMPORTANT: At this point, copy/cut the .PFX certificate file saved in the downloads forlder and save it in a secure place.
+
## Install the certificate
-Install the certificate under 'Current User' store location and check it as exportable.
+Install the certificate (by double-clicking on the .PFX file) under 'Current User' store location (by default location) and check it as exportable.
+
## Generate a certificate in Azure Keyvault
-Execute the gen-keyvaultcert.ps1 script to generate and download a certificate from Keyvault.
+In a POWER-SHELL window, move to the folder [..\deploy\az\servicefabric\WindowsContainers](https://github.com/dotnet-architecture/eShopOnContainers/tree/dev/deploy/az/servicefabric/WindowsContainers).
+
+**Select your Azure subscription** You might have [several Azure subscriptions](https://docs.microsoft.com/en-us/cli/azure/account#set) as shown if you type the following.
+
+ >```
+ >az account list
+ >```
+ If you have multiple subscription accounts, you first need to select the Azure subscription account you want to target. Type the following:
+ >```
+ >az account set --subscription "Your Azure Subscription Name or ID"
+ >```
+
+**Execute the gen-keyvaultcert.ps1 script** to generate and download a certificate from Keyvault.
+Make sure you're going to run it against the Azure subscription you mean it.
+
+You might need to authenticate from the browser when running this PowerShell script.
```
-.\gen-keyvaultcert.ps1 -vaultName -certName -certPwd -subjectName CN=.westeurope.cloudapp.azure.com -saveDir C:\Users\\Downloads
+.\gen-keyvaultcert.ps1 -vaultName -certName -certPwd -subjectName CN=.westus.cloudapp.azure.com -saveDir C:\Users\\Downloads
```
+You should see a similar execution to the following:
+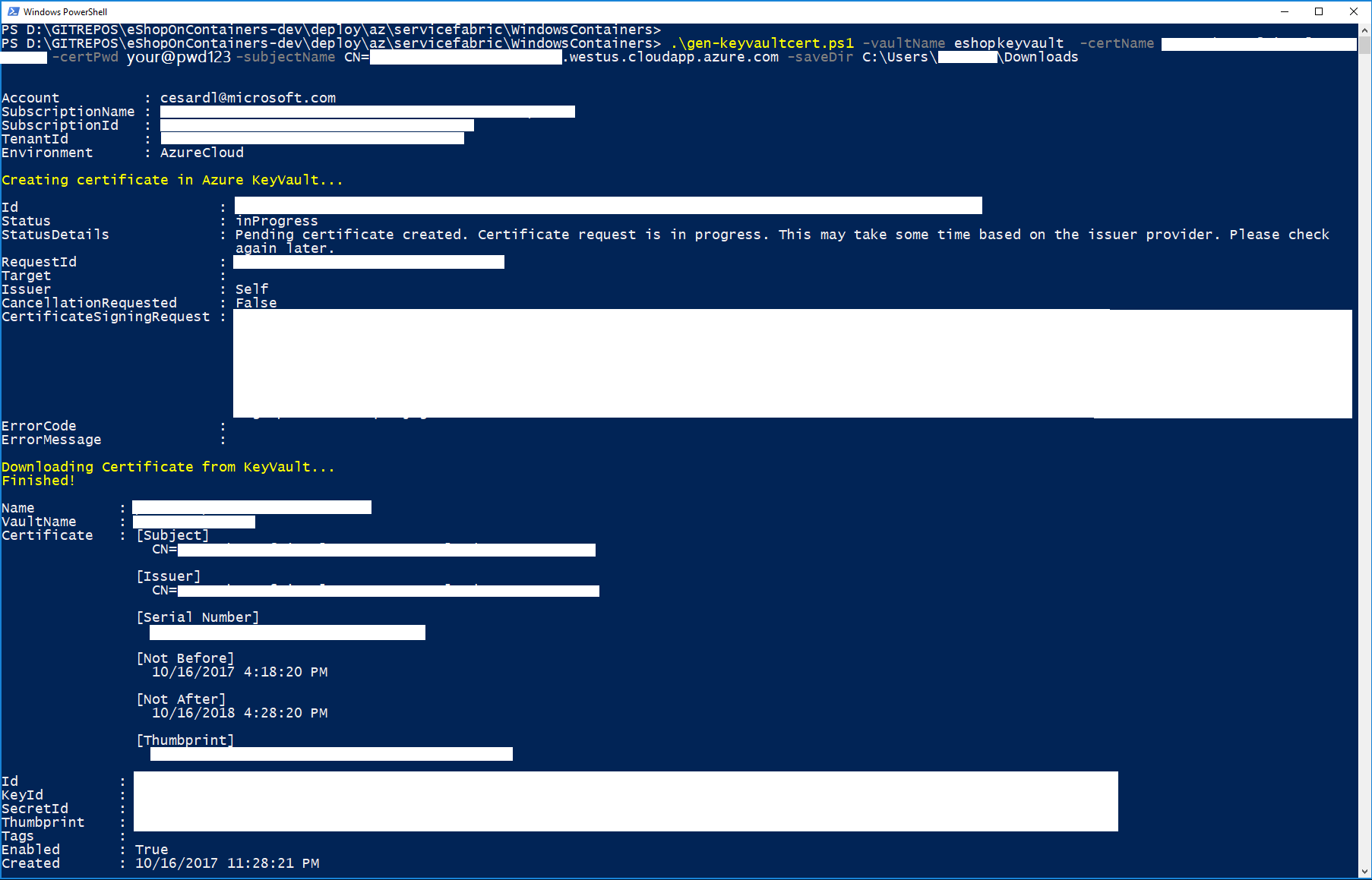
+
+IMPORTANT: At this point, copy/cut the .PFX certificate file saved in the downloads forlder and save it in a secure place.
+
## Install the certificate
-Install the certificate under 'Current User' store location and check it as exportable.
+Install the certificate (by double-clicking on the .PFX file) under 'Current User' store location (by default location) and check it as exportable.
 +Also, install the same certificate as CA (Certificate Authority) under Current User, too.
+
+
+
## Editing servicefabricdeploysecured.parameters.json file
-Edit the following params in `servicefabricdeploysecured.parameters.json` file to set your values:
+Edit the parameters in `servicefabricdeploysecured.parameters.json` in a similar way you can do with the unsecured .json file shown above (clusterName, dnsName, etc.), plus edit the following values:
-- clusterName: Name of your SF cluster
-- dnsName: Name assigned to your SF dns
-- adminUserName: user name for administration
-- adminPassword: user password for administration
-- sourceVaultValue: keyvault resource id (check azure keyvault properties)
-- certificateUrlValue: certificate url (check azure Keyvault certificate properties)
-- certificateThumbprint: certificate thumbprint (check azure Keyvault certificate properties)
+- sourceVaultValue: Your Azure Keyvault's RESOURCE ID (check Azure keyvault properties, similar to: /subscriptions/e1234ac1-c09c-3jaf-6767-98b3c5f1f246/resourceGroups/eshop-global-resgrp/providers/Microsoft.KeyVault/vaults/eshopkeyvault")
-Optionally, you can modify which ports are opened in the LoadBalancer for accessing externally to the apps:
+- certificateUrlValue: Your certificate Secret Identifier (check Azure Keyvault secret certificate properties, should be in the format of https://.vault.azure.net:443/secrets/, similar to:
+https://eshopkeyvault.vault.azure.net/secrets/pro-eshop-sfwin-cluster-cert/w647684642cGE2sj83b3hfe4h8e08963)
-- webMvcHttpPort: port externally exposed for the WebMVC app
-- webSpaHttpPort: port externally exposed for the WebSPA app
-- webStatusHttpPort: port externally exposed for the WebStatus app
-- IdSrvHttpRule: port externally exposed for the Identity app
+- certificateThumbprint: certificate thumbprint (check azure Keyvault certificate thumbprint, something like 88JK453486D55A6818573G0DW9100365HDK70HDK)
-## Deploy the template
+## Deploy the secured SF cluster (Windows nodes)
-Once parameter file is edited you can deploy it using [create-resources script](../readme.md).
+Once parameters file is edited you can deploy it using [create-resources script](../readme.md).
+
+Use a command prompt window positioned into the deploy\az folder.
```
-create-resources.cmd servicefabric\WindowsContainers\servicefabricdeploysecured newResourceGroup -c westus
+create-resources.cmd servicefabric\WindowsContainers\servicefabricdeploysecured pro-eshop-sfwin-resgrp -c westus
```
-## Deploy eShopOnServiceFabric with Visual Studio.
+The execution should be something like the following:
+
+
+
+Once the cluster is created you can explore it with Azure's portal, like in the following image:
+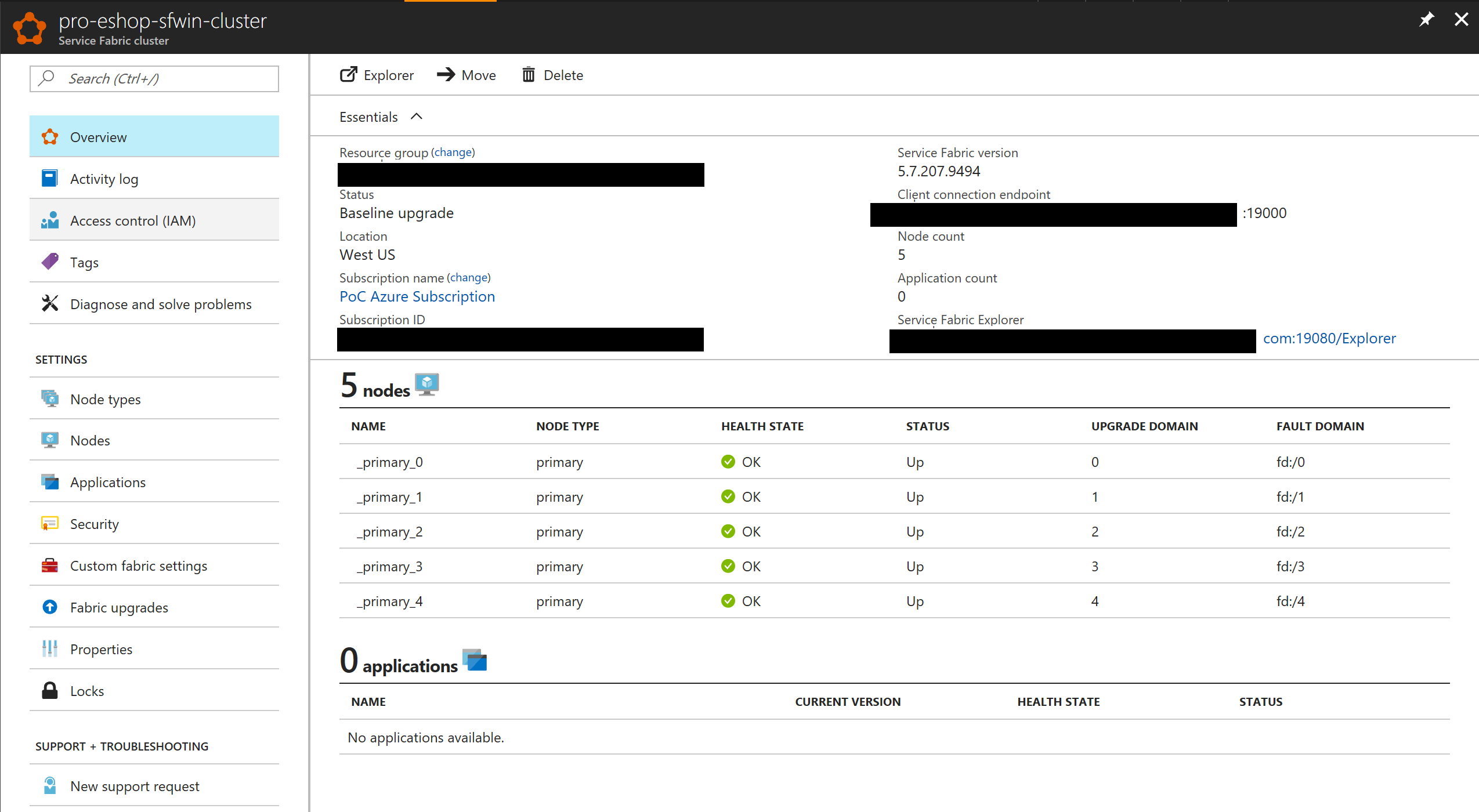
+
+In this case, the ARM template is creating a 5 node cluster when creating a SECURE cluster for "production".
+
+
+# Deploy eShopOnServiceFabric with Visual Studio.
Modify the cloud.xml file of each Service Fabric application in PublishProfile directory and set your certificate settings to be able to deploy eshopOnContainers in the secured cluster:
diff --git a/deploy/az/servicefabric/WindowsContainers/servicefabricdeploy.parameters.json b/deploy/az/servicefabric/WindowsContainers/servicefabricdeploy.parameters.json
index bf1b89642..2c214b754 100644
--- a/deploy/az/servicefabric/WindowsContainers/servicefabricdeploy.parameters.json
+++ b/deploy/az/servicefabric/WindowsContainers/servicefabricdeploy.parameters.json
@@ -3,19 +3,19 @@
"contentVersion": "1.0.0.0",
"parameters": {
"clusterName": {
- "value": "eshoponservicefabric"
+ "value": "qa-eshop-sfwin-cluster"
},
"clusterLocation": {
- "value": "westeurope"
+ "value": "westus"
},
"computeLocation": {
- "value": "westeurope"
+ "value": "westus"
},
"adminUserName": {
"value": "eshop"
},
"adminPassword": {
- "value": "your_password"
+ "value": "Your_complex_Pass@word1"
},
"nicName": {
"value": "NIC-eshopsfwin"
@@ -24,7 +24,7 @@
"value": "eshopsfwin-PubIP"
},
"dnsName": {
- "value": "eshoponservicefabric"
+ "value": "qa-eshop-sfwin-cluster"
},
"virtualNetworkName": {
"value": "VNet-eshopsfwin"
@@ -36,10 +36,10 @@
"value": "LBIP-eshopsfwin"
},
"applicationDiagnosticsStorageAccountName": {
- "value": "sfdgeshopsfwin6744"
+ "value": "sfdgqaeshopsfwin"
},
"supportLogStorageAccountName": {
- "value": "sflogseshopsfwin3480"
+ "value": "sflogsqaeshopsfwin"
},
"vmImageSku": {
"value": "2016-Datacenter-with-Containers"
diff --git a/deploy/az/servicefabric/WindowsContainers/servicefabricdeploysecured.parameters.json b/deploy/az/servicefabric/WindowsContainers/servicefabricdeploysecured.parameters.json
index 2092ebd9a..bbc8eb663 100644
--- a/deploy/az/servicefabric/WindowsContainers/servicefabricdeploysecured.parameters.json
+++ b/deploy/az/servicefabric/WindowsContainers/servicefabricdeploysecured.parameters.json
@@ -3,19 +3,19 @@
"contentVersion": "1.0.0.0",
"parameters": {
"clusterName": {
- "value": "your_sf_name"
+ "value": "pro-eshop-sfwin-cluster"
},
"clusterLocation": {
- "value": "westeurope"
+ "value": "westus"
},
"computeLocation": {
- "value": "westeurope"
+ "value": "westus"
},
"adminUserName": {
"value": "eshop"
},
"adminPassword": {
- "value": "your_admin_password"
+ "value": "Your_complex_Pass@word1"
},
"nicName": {
"value": "NIC-eshopsfwin"
@@ -24,7 +24,7 @@
"value": "eshopsfwin-PubIP"
},
"dnsName": {
- "value": "your_sf_dns"
+ "value": "pro-eshop-sfwin-cluster"
},
"virtualNetworkName": {
"value": "VNet-eshopsfwin"
@@ -36,19 +36,19 @@
"value": "LBIP-eshopsfwin"
},
"applicationDiagnosticsStorageAccountName": {
- "value": "sfdgeshopsfwin6744"
+ "value": "sfdgqaeshopsfwinsec"
},
"supportLogStorageAccountName": {
- "value": "sflogseshopsfwin3480"
+ "value": "sflogsqaeshopsfwinsec"
},
"sourceVaultValue": {
- "value": ""
+ "value": "your-value-check-keyvault-at-azure"
},
"certificateUrlValue": {
- "value": ""
+ "value": "your-value-check-keyvault-at-azure"
},
"certificateThumbprint": {
- "value": ""
+ "value": "your-value-check-keyvault-at-azure"
},
"vmImageSku": {
"value": "2016-Datacenter-with-Containers"
+Also, install the same certificate as CA (Certificate Authority) under Current User, too.
+
+
+
## Editing servicefabricdeploysecured.parameters.json file
-Edit the following params in `servicefabricdeploysecured.parameters.json` file to set your values:
+Edit the parameters in `servicefabricdeploysecured.parameters.json` in a similar way you can do with the unsecured .json file shown above (clusterName, dnsName, etc.), plus edit the following values:
-- clusterName: Name of your SF cluster
-- dnsName: Name assigned to your SF dns
-- adminUserName: user name for administration
-- adminPassword: user password for administration
-- sourceVaultValue: keyvault resource id (check azure keyvault properties)
-- certificateUrlValue: certificate url (check azure Keyvault certificate properties)
-- certificateThumbprint: certificate thumbprint (check azure Keyvault certificate properties)
+- sourceVaultValue: Your Azure Keyvault's RESOURCE ID (check Azure keyvault properties, similar to: /subscriptions/e1234ac1-c09c-3jaf-6767-98b3c5f1f246/resourceGroups/eshop-global-resgrp/providers/Microsoft.KeyVault/vaults/eshopkeyvault")
-Optionally, you can modify which ports are opened in the LoadBalancer for accessing externally to the apps:
+- certificateUrlValue: Your certificate Secret Identifier (check Azure Keyvault secret certificate properties, should be in the format of https://.vault.azure.net:443/secrets/, similar to:
+https://eshopkeyvault.vault.azure.net/secrets/pro-eshop-sfwin-cluster-cert/w647684642cGE2sj83b3hfe4h8e08963)
-- webMvcHttpPort: port externally exposed for the WebMVC app
-- webSpaHttpPort: port externally exposed for the WebSPA app
-- webStatusHttpPort: port externally exposed for the WebStatus app
-- IdSrvHttpRule: port externally exposed for the Identity app
+- certificateThumbprint: certificate thumbprint (check azure Keyvault certificate thumbprint, something like 88JK453486D55A6818573G0DW9100365HDK70HDK)
-## Deploy the template
+## Deploy the secured SF cluster (Windows nodes)
-Once parameter file is edited you can deploy it using [create-resources script](../readme.md).
+Once parameters file is edited you can deploy it using [create-resources script](../readme.md).
+
+Use a command prompt window positioned into the deploy\az folder.
```
-create-resources.cmd servicefabric\WindowsContainers\servicefabricdeploysecured newResourceGroup -c westus
+create-resources.cmd servicefabric\WindowsContainers\servicefabricdeploysecured pro-eshop-sfwin-resgrp -c westus
```
-## Deploy eShopOnServiceFabric with Visual Studio.
+The execution should be something like the following:
+
+
+
+Once the cluster is created you can explore it with Azure's portal, like in the following image:
+
+
+In this case, the ARM template is creating a 5 node cluster when creating a SECURE cluster for "production".
+
+
+# Deploy eShopOnServiceFabric with Visual Studio.
Modify the cloud.xml file of each Service Fabric application in PublishProfile directory and set your certificate settings to be able to deploy eshopOnContainers in the secured cluster:
diff --git a/deploy/az/servicefabric/WindowsContainers/servicefabricdeploy.parameters.json b/deploy/az/servicefabric/WindowsContainers/servicefabricdeploy.parameters.json
index bf1b89642..2c214b754 100644
--- a/deploy/az/servicefabric/WindowsContainers/servicefabricdeploy.parameters.json
+++ b/deploy/az/servicefabric/WindowsContainers/servicefabricdeploy.parameters.json
@@ -3,19 +3,19 @@
"contentVersion": "1.0.0.0",
"parameters": {
"clusterName": {
- "value": "eshoponservicefabric"
+ "value": "qa-eshop-sfwin-cluster"
},
"clusterLocation": {
- "value": "westeurope"
+ "value": "westus"
},
"computeLocation": {
- "value": "westeurope"
+ "value": "westus"
},
"adminUserName": {
"value": "eshop"
},
"adminPassword": {
- "value": "your_password"
+ "value": "Your_complex_Pass@word1"
},
"nicName": {
"value": "NIC-eshopsfwin"
@@ -24,7 +24,7 @@
"value": "eshopsfwin-PubIP"
},
"dnsName": {
- "value": "eshoponservicefabric"
+ "value": "qa-eshop-sfwin-cluster"
},
"virtualNetworkName": {
"value": "VNet-eshopsfwin"
@@ -36,10 +36,10 @@
"value": "LBIP-eshopsfwin"
},
"applicationDiagnosticsStorageAccountName": {
- "value": "sfdgeshopsfwin6744"
+ "value": "sfdgqaeshopsfwin"
},
"supportLogStorageAccountName": {
- "value": "sflogseshopsfwin3480"
+ "value": "sflogsqaeshopsfwin"
},
"vmImageSku": {
"value": "2016-Datacenter-with-Containers"
diff --git a/deploy/az/servicefabric/WindowsContainers/servicefabricdeploysecured.parameters.json b/deploy/az/servicefabric/WindowsContainers/servicefabricdeploysecured.parameters.json
index 2092ebd9a..bbc8eb663 100644
--- a/deploy/az/servicefabric/WindowsContainers/servicefabricdeploysecured.parameters.json
+++ b/deploy/az/servicefabric/WindowsContainers/servicefabricdeploysecured.parameters.json
@@ -3,19 +3,19 @@
"contentVersion": "1.0.0.0",
"parameters": {
"clusterName": {
- "value": "your_sf_name"
+ "value": "pro-eshop-sfwin-cluster"
},
"clusterLocation": {
- "value": "westeurope"
+ "value": "westus"
},
"computeLocation": {
- "value": "westeurope"
+ "value": "westus"
},
"adminUserName": {
"value": "eshop"
},
"adminPassword": {
- "value": "your_admin_password"
+ "value": "Your_complex_Pass@word1"
},
"nicName": {
"value": "NIC-eshopsfwin"
@@ -24,7 +24,7 @@
"value": "eshopsfwin-PubIP"
},
"dnsName": {
- "value": "your_sf_dns"
+ "value": "pro-eshop-sfwin-cluster"
},
"virtualNetworkName": {
"value": "VNet-eshopsfwin"
@@ -36,19 +36,19 @@
"value": "LBIP-eshopsfwin"
},
"applicationDiagnosticsStorageAccountName": {
- "value": "sfdgeshopsfwin6744"
+ "value": "sfdgqaeshopsfwinsec"
},
"supportLogStorageAccountName": {
- "value": "sflogseshopsfwin3480"
+ "value": "sflogsqaeshopsfwinsec"
},
"sourceVaultValue": {
- "value": ""
+ "value": "your-value-check-keyvault-at-azure"
},
"certificateUrlValue": {
- "value": ""
+ "value": "your-value-check-keyvault-at-azure"
},
"certificateThumbprint": {
- "value": ""
+ "value": "your-value-check-keyvault-at-azure"
},
"vmImageSku": {
"value": "2016-Datacenter-with-Containers"
 +You should see a similar execution to the following:
+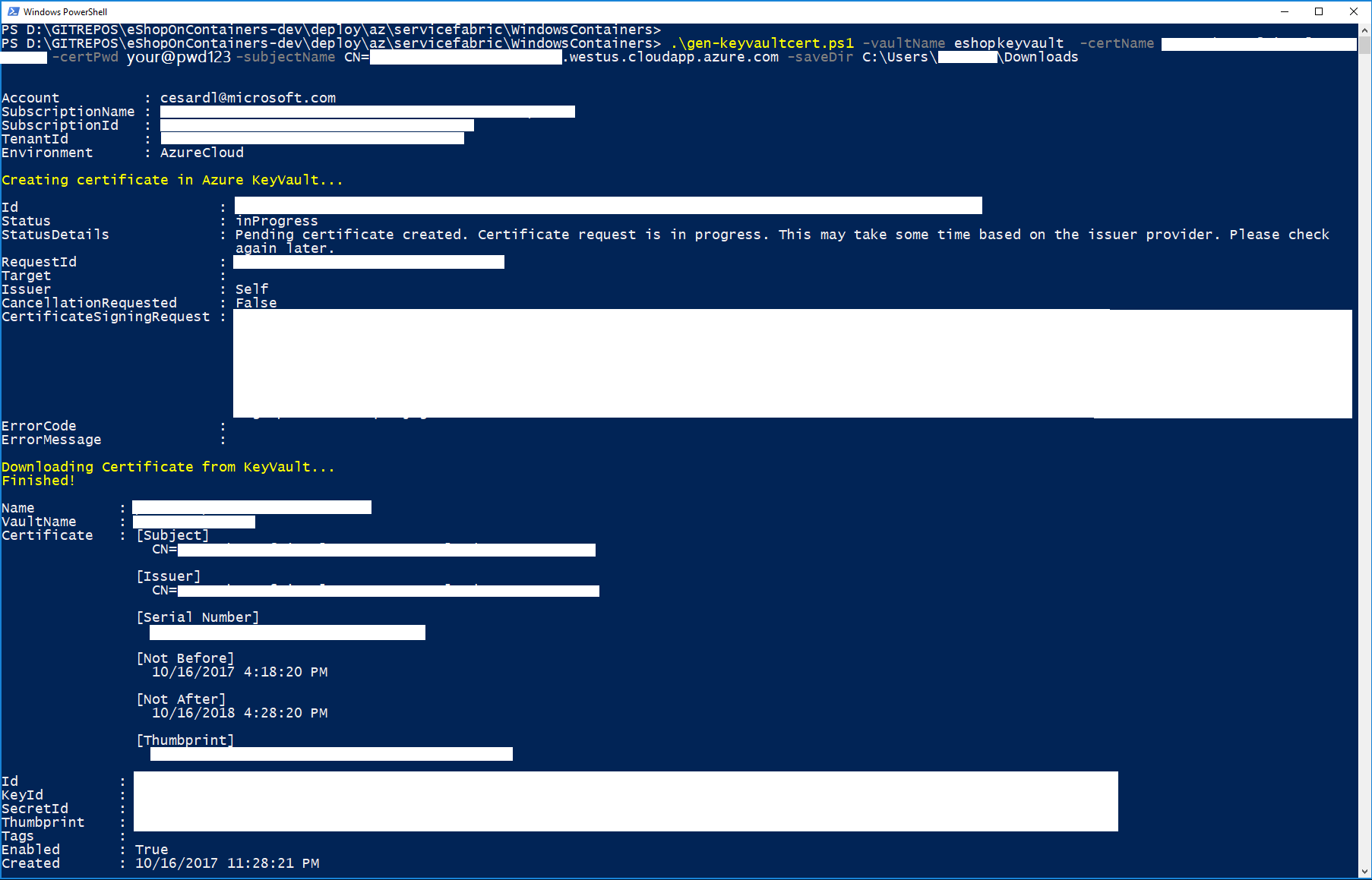
+
+IMPORTANT: At this point, copy/cut the .PFX certificate file saved in the downloads forlder and save it in a secure place.
+
+## Install the certificate
+Install the certificate (by double-clicking on the .PFX file) under 'Current User' store location (by default location) and check it as exportable.
+
+
+You should see a similar execution to the following:
+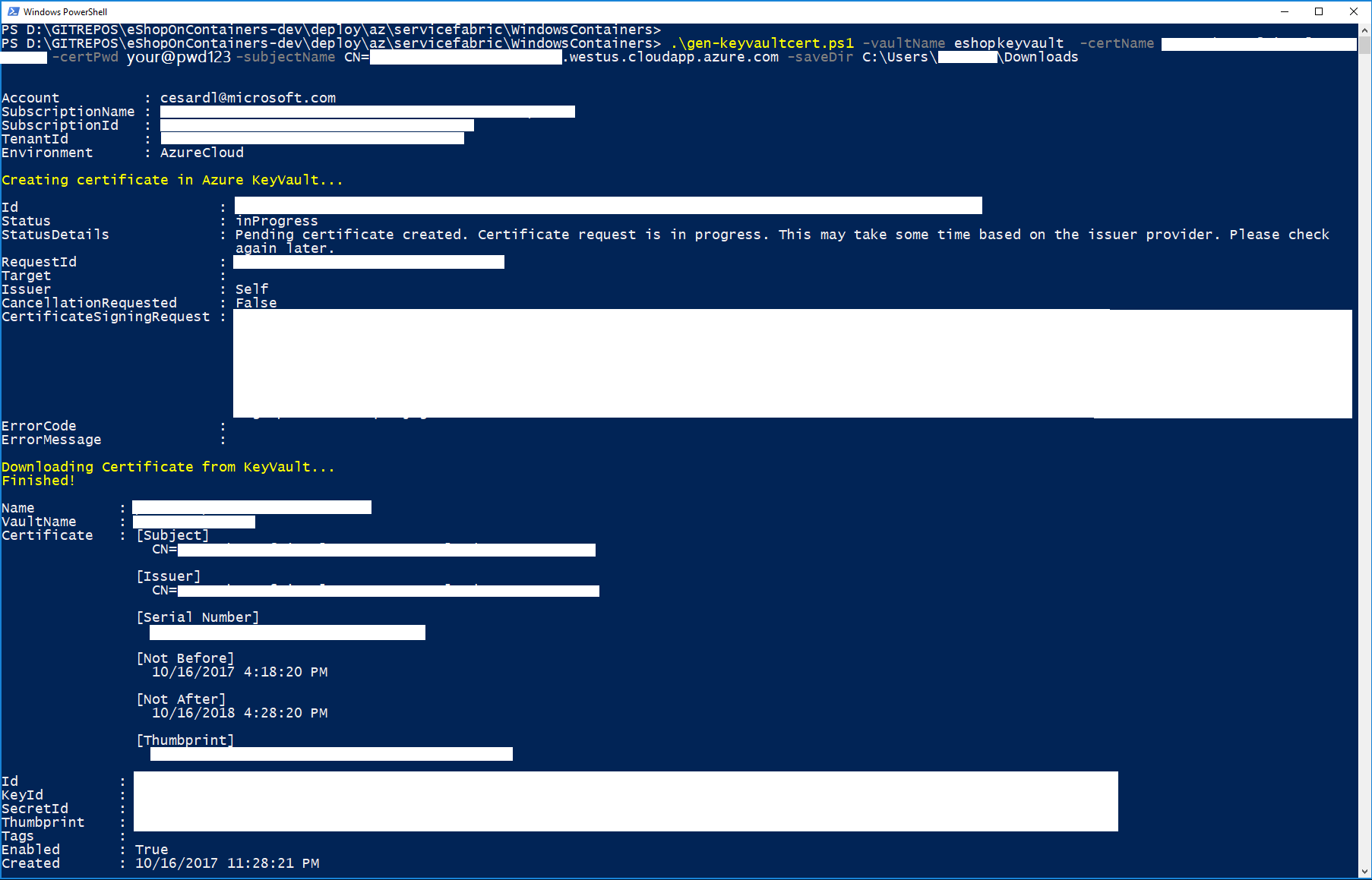
+
+IMPORTANT: At this point, copy/cut the .PFX certificate file saved in the downloads forlder and save it in a secure place.
+
+## Install the certificate
+Install the certificate (by double-clicking on the .PFX file) under 'Current User' store location (by default location) and check it as exportable.
+
+ +
+Also, install the same certificate as CA (Certificate Authority) under Current User, too.
+
+
## Editing servicefabricdeploysecured.parameters.json file
-Edit the following params in `servicefabricdeploysecured.parameters.json` file to set your values:
+Edit the parameters in `servicefabricdeploysecured.parameters.json` in a similar way you can do with the unsecured .json file shown above (clusterName, dnsName, etc.), plus edit the following values:
-- clusterName: Name of your SF cluster
-- dnsName: Name assigned to your SF dns
-- adminUserName: user name for administration
-- adminPassword: user password for administration
-- sourceVaultValue: keyvault resource id (check azure keyvault properties)
-- certificateUrlValue: certificate url (check azure Keyvault certificate properties)
-- certificateThumbprint: certificate thumbprint (check azure Keyvault certificate properties)
+- sourceVaultValue: Your Azure Keyvault's RESOURCE ID (check Azure keyvault properties, similar to: /subscriptions/e1234ac1-c09c-3jaf-6767-98b3c5f1f246/resourceGroups/eshop-global-resgrp/providers/Microsoft.KeyVault/vaults/eshopkeyvault")
-Optionally, you can modify which ports are opened in the LoadBalancer for accessing externally to the apps:
+- certificateUrlValue: Your certificate Secret Identifier (check Azure Keyvault secret certificate properties, should be in the format of https://
+
+Also, install the same certificate as CA (Certificate Authority) under Current User, too.
+
+
## Editing servicefabricdeploysecured.parameters.json file
-Edit the following params in `servicefabricdeploysecured.parameters.json` file to set your values:
+Edit the parameters in `servicefabricdeploysecured.parameters.json` in a similar way you can do with the unsecured .json file shown above (clusterName, dnsName, etc.), plus edit the following values:
-- clusterName: Name of your SF cluster
-- dnsName: Name assigned to your SF dns
-- adminUserName: user name for administration
-- adminPassword: user password for administration
-- sourceVaultValue: keyvault resource id (check azure keyvault properties)
-- certificateUrlValue: certificate url (check azure Keyvault certificate properties)
-- certificateThumbprint: certificate thumbprint (check azure Keyvault certificate properties)
+- sourceVaultValue: Your Azure Keyvault's RESOURCE ID (check Azure keyvault properties, similar to: /subscriptions/e1234ac1-c09c-3jaf-6767-98b3c5f1f246/resourceGroups/eshop-global-resgrp/providers/Microsoft.KeyVault/vaults/eshopkeyvault")
-Optionally, you can modify which ports are opened in the LoadBalancer for accessing externally to the apps:
+- certificateUrlValue: Your certificate Secret Identifier (check Azure Keyvault secret certificate properties, should be in the format of https:// +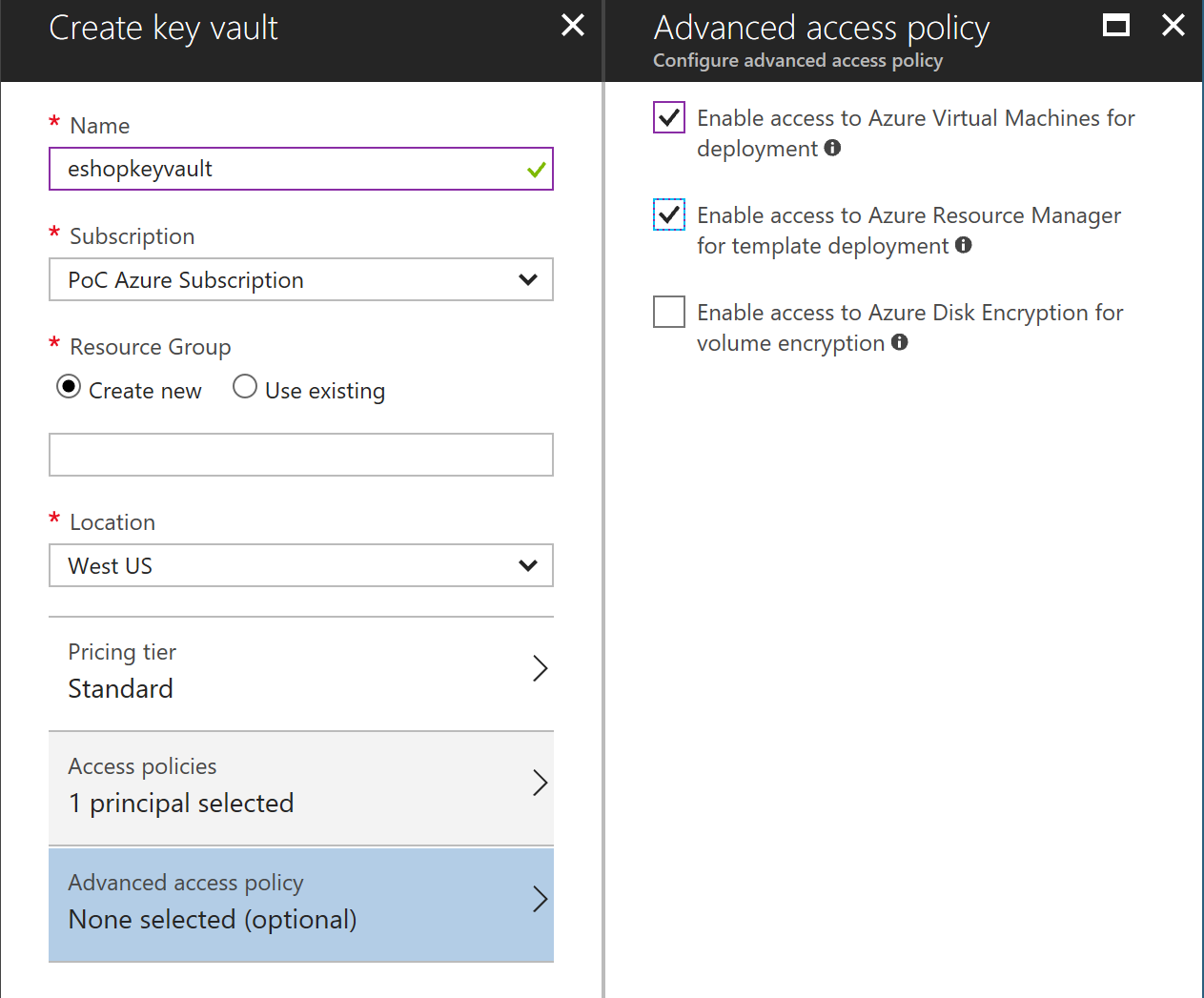
## Generate a certificate in Azure Keyvault
-Execute the gen-keyvaultcert.ps1 script to generate and download a certificate from Keyvault.
+In a POWER-SHELL window, move to the folder [..\deploy\az\servicefabric\WindowsContainers](https://github.com/dotnet-architecture/eShopOnContainers/tree/dev/deploy/az/servicefabric/WindowsContainers).
+
+**Select your Azure subscription** You might have [several Azure subscriptions](https://docs.microsoft.com/en-us/cli/azure/account#set) as shown if you type the following.
+
+ >```
+ >az account list
+ >```
+ If you have multiple subscription accounts, you first need to select the Azure subscription account you want to target. Type the following:
+ >```
+ >az account set --subscription "Your Azure Subscription Name or ID"
+ >```
+
+**Execute the gen-keyvaultcert.ps1 script** to generate and download a certificate from Keyvault.
+Make sure you're going to run it against the Azure subscription you mean it.
+
+You might need to authenticate from the browser when running this PowerShell script.
```
-.\gen-keyvaultcert.ps1 -vaultName
+
## Generate a certificate in Azure Keyvault
-Execute the gen-keyvaultcert.ps1 script to generate and download a certificate from Keyvault.
+In a POWER-SHELL window, move to the folder [..\deploy\az\servicefabric\WindowsContainers](https://github.com/dotnet-architecture/eShopOnContainers/tree/dev/deploy/az/servicefabric/WindowsContainers).
+
+**Select your Azure subscription** You might have [several Azure subscriptions](https://docs.microsoft.com/en-us/cli/azure/account#set) as shown if you type the following.
+
+ >```
+ >az account list
+ >```
+ If you have multiple subscription accounts, you first need to select the Azure subscription account you want to target. Type the following:
+ >```
+ >az account set --subscription "Your Azure Subscription Name or ID"
+ >```
+
+**Execute the gen-keyvaultcert.ps1 script** to generate and download a certificate from Keyvault.
+Make sure you're going to run it against the Azure subscription you mean it.
+
+You might need to authenticate from the browser when running this PowerShell script.
```
-.\gen-keyvaultcert.ps1 -vaultName  +Also, install the same certificate as CA (Certificate Authority) under Current User, too.
+
+
+
## Editing servicefabricdeploysecured.parameters.json file
-Edit the following params in `servicefabricdeploysecured.parameters.json` file to set your values:
+Edit the parameters in `servicefabricdeploysecured.parameters.json` in a similar way you can do with the unsecured .json file shown above (clusterName, dnsName, etc.), plus edit the following values:
-- clusterName: Name of your SF cluster
-- dnsName: Name assigned to your SF dns
-- adminUserName: user name for administration
-- adminPassword: user password for administration
-- sourceVaultValue: keyvault resource id (check azure keyvault properties)
-- certificateUrlValue: certificate url (check azure Keyvault certificate properties)
-- certificateThumbprint: certificate thumbprint (check azure Keyvault certificate properties)
+- sourceVaultValue: Your Azure Keyvault's RESOURCE ID (check Azure keyvault properties, similar to: /subscriptions/e1234ac1-c09c-3jaf-6767-98b3c5f1f246/resourceGroups/eshop-global-resgrp/providers/Microsoft.KeyVault/vaults/eshopkeyvault")
-Optionally, you can modify which ports are opened in the LoadBalancer for accessing externally to the apps:
+- certificateUrlValue: Your certificate Secret Identifier (check Azure Keyvault secret certificate properties, should be in the format of https://
+Also, install the same certificate as CA (Certificate Authority) under Current User, too.
+
+
+
## Editing servicefabricdeploysecured.parameters.json file
-Edit the following params in `servicefabricdeploysecured.parameters.json` file to set your values:
+Edit the parameters in `servicefabricdeploysecured.parameters.json` in a similar way you can do with the unsecured .json file shown above (clusterName, dnsName, etc.), plus edit the following values:
-- clusterName: Name of your SF cluster
-- dnsName: Name assigned to your SF dns
-- adminUserName: user name for administration
-- adminPassword: user password for administration
-- sourceVaultValue: keyvault resource id (check azure keyvault properties)
-- certificateUrlValue: certificate url (check azure Keyvault certificate properties)
-- certificateThumbprint: certificate thumbprint (check azure Keyvault certificate properties)
+- sourceVaultValue: Your Azure Keyvault's RESOURCE ID (check Azure keyvault properties, similar to: /subscriptions/e1234ac1-c09c-3jaf-6767-98b3c5f1f246/resourceGroups/eshop-global-resgrp/providers/Microsoft.KeyVault/vaults/eshopkeyvault")
-Optionally, you can modify which ports are opened in the LoadBalancer for accessing externally to the apps:
+- certificateUrlValue: Your certificate Secret Identifier (check Azure Keyvault secret certificate properties, should be in the format of https:// +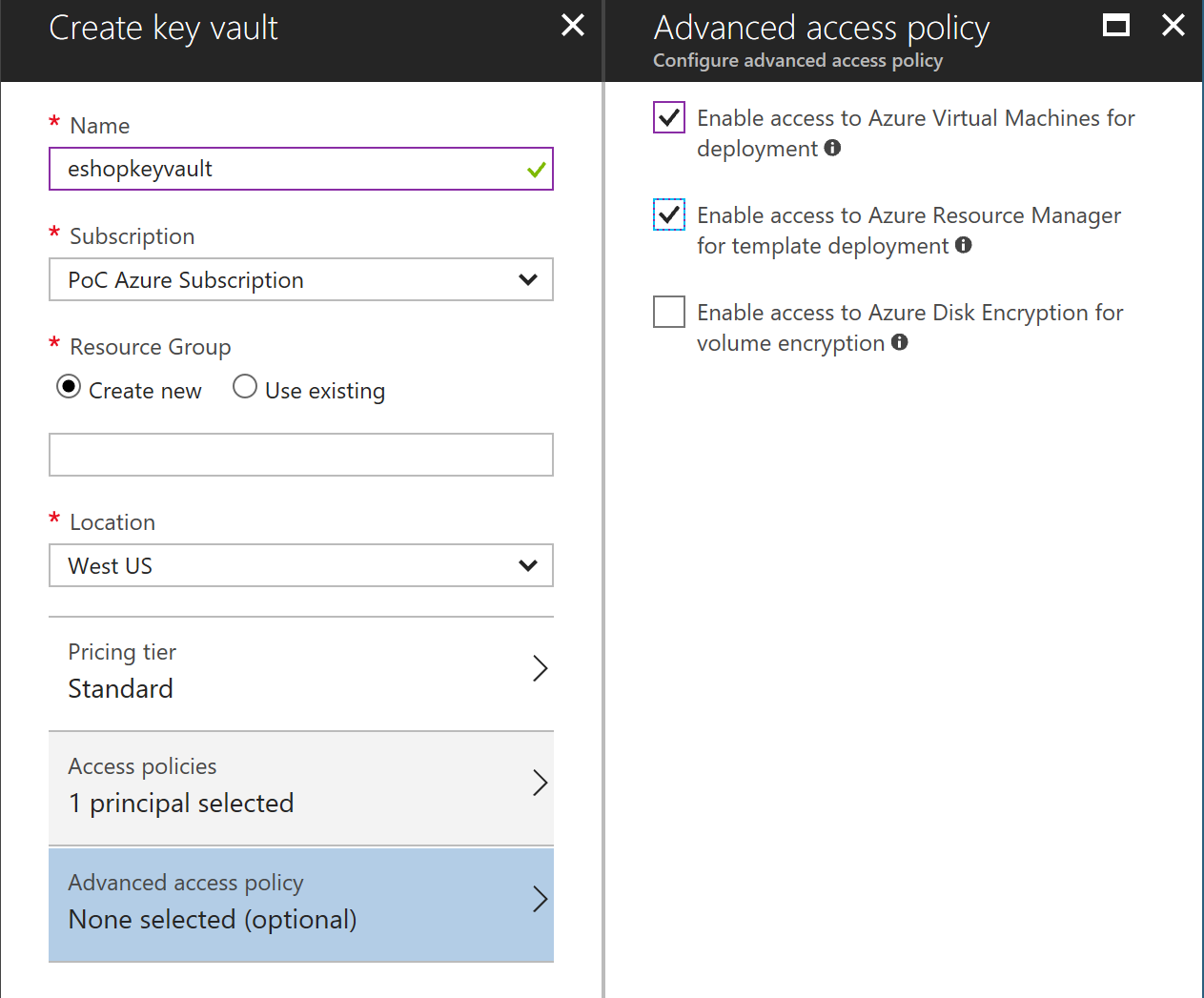
## Generate a certificate in Azure Keyvault
+In a POWER-SHELL window, move to the folder [..\deploy\az\servicefabric\LinuxContainers](https://github.com/dotnet-architecture/eShopOnContainers/tree/dev/deploy/az/servicefabric/LinuxContainers).
+
+**Select your Azure subscription** You might have [several Azure subscriptions](https://docs.microsoft.com/en-us/cli/azure/account#set) as shown if you type the following.
+
+ >```
+ >az account list
+ >```
+ If you have multiple subscription accounts, you first need to select the Azure subscription account you want to target. Type the following:
+ >```
+ >az account set --subscription "Your Azure Subscription Name or ID"
+ >```
+
Execute the gen-keyvaultcert.ps1 script to generate and download a certificate from Keyvault.
```
.\gen-keyvaultcert.ps1 -vaultName
+
## Generate a certificate in Azure Keyvault
+In a POWER-SHELL window, move to the folder [..\deploy\az\servicefabric\LinuxContainers](https://github.com/dotnet-architecture/eShopOnContainers/tree/dev/deploy/az/servicefabric/LinuxContainers).
+
+**Select your Azure subscription** You might have [several Azure subscriptions](https://docs.microsoft.com/en-us/cli/azure/account#set) as shown if you type the following.
+
+ >```
+ >az account list
+ >```
+ If you have multiple subscription accounts, you first need to select the Azure subscription account you want to target. Type the following:
+ >```
+ >az account set --subscription "Your Azure Subscription Name or ID"
+ >```
+
Execute the gen-keyvaultcert.ps1 script to generate and download a certificate from Keyvault.
```
.\gen-keyvaultcert.ps1 -vaultName